We all like to have a short yet meaningful domain names for our website or blog. But searching for available domains on GoDaddy or Big Rock is very time consuming and frustrating. In my case, I wanted a simple domain name related to programming. I searched and searched. Finally bought www.genuinecoder.comfrom GoDaddy. The truth is, I named this blog as Genuine Coder after purchasing the domain name.
Author: Muhammed Afsal Villan
-

Find Perfect Domain Name with Domain Suggestion Tools
So that’s not your case, right? Well, there are a number of ways to find out available domain names. Let’s see how we can find a perfect domain name for you.Lean domain search asks to enter a word that you want your domain name to include. I have used “programming” and got 3,875 available domains. Lean domain search provides options to sort result according to popularity, length or alphabetical order. Moreover, it searches on twitter to find out whether “@yourdomain” is available on twitter.Lean domain search also provides Search Term Filter that helps to filter the result based on domain names starting with search term or ending with search term.Domains bot work like Lean domain search. Once you enter a keyword, you will get list of available domains. You can choose whether you want particular TLD (Top Level Domain) like .com, .org etc. It is also possible to choose the words from English, Deutsch, Español, Italiano, Français and Dutch.Name Mesh is also a good choice. Simply enter in your keywords and results will be sorted into eight categories of results, including Common, New, Short, Extra, Similar, SEO, Fun and Mix. You can refine your result by limiting the maximum characters or showing only ones that available with particular registrar like GoDaddy or BlueHost.Domainr is a simple tool to find available domains. It has less options compared to above ones. When you search for a specific keyword in domainr, you will get a list of .com, .org, .co.in etc variations. Unlike above tools, it does not provide any added keywords as prefix and suffix.I searched for eye and got eye.com, eye.net etc. as taken and eye.org for sale.It is better to do a thorough research before buying a domain. Because After setting one domain for your website/blog, it is hard to change since all the search engine entries and back-links will be lost. Moreover, you will loose your precious Alexa ranking too.All of these tools are very helpful. Yet, I prefer LeanDomainSearch and NameMesh since they have a lot of search refining options. -
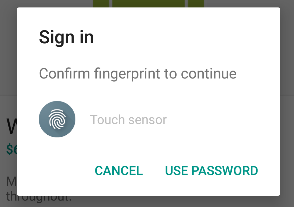
Emulating Fingerprint in Android Emulator
Android Emulators are simply the best way to test our application during development or when we want to use apps on PC. Currently, fingerprint smartphones are not that common, but surely, it will become one of the basic features like Bluetooth or Camera. So it is necessary to start making maximum use of the fingerprint scanner.
Android Fingerprint Prompt When i started developing applications with a fingerprint scanner, I had to find a way to emulate the scanner in my emulator. Thanks to Android Developer website.Before explaining how to Emulate a fingerprint scanner, you have to make sure that the following requirements are satisfied in your system.- Currently, the Fingerprint API is only supported from Marshmallow. Make sure your emulator is running on Android M (API 23) or better.
- Android SDK Tools Revision 24.3 or better.
Watch my video on How to use fingerprint for emulatorSteps for adding Fingerprint in Android Emulator
- Activate Screen lock from Settings -> Security. Then Go to Fingerprint option to add new fingerprint

- When prompt to place your finger on the scanner, emulate the fingerprint using ADB command.

Android Fingerprint Authentication adb -e emu finger touch <finger_id> #Example adb -e emu finger touch 1155aa1155- You should see fingerprint detected message. That’s it. Done.

- Whenever an application prompts for fingerprint, just use the previously used ADB command with the given finger_id to authenticate.
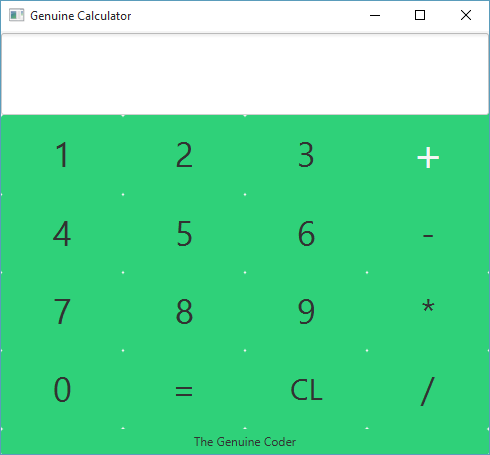
Making Calculator in JavaFX (with Source Code)
JavaFX is a wonderful improvement to Java programming language. It includes a wide number of new user interface controls and the ability to add cascade style sheets (CSS), Animations etc. Today, Let’s see how we can build a beautiful calculator in JavaFX with CSS styling. This tutorial is done using NetBeans IDE and JavaFX Scene Builder 2.0. Watch The Complete Tutorial Video below.Part 1 : User Interface Design and Event Handling
Part 2 : Adding CSS
Get This Project
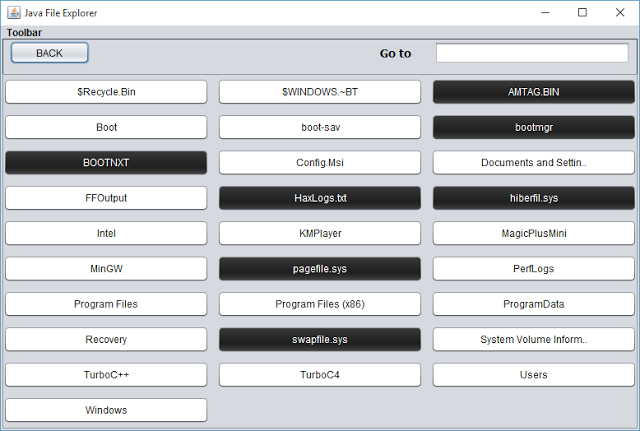
Java File Explorer program with Source Code
Let’s develop a basic file explorer using java. Java’s FILE class from java.io package provides simple way to represent both files and directories. That means, the same class can represent both files and directories.This program starts by creating a new file in the root. For example we can start at C drive in windows or root(/) in Linux.
File f = new File(“C:\”);
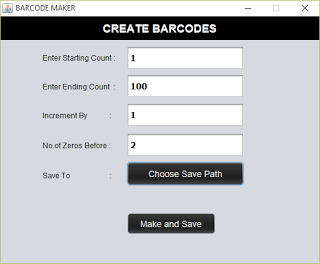
The list of available files and folders present in the given directory can be accessed using the function listFiles(). It returns a list of files pointing to the contents inside the directory. Using a for loop buttons are created dynamically for each of these files and added to the container panel.Handling FilesThe button can be either file or folder. Using isFile() function in the FILE class, it is possible to determine whether a file is a file or directory. If it is a file, we then have to open it, if possible.Java provides a powerful handle to the operating system using ‘Desktop’ class from java.awt package. Using Desktop we can open a file using the default program associated for it.Desktop.getDesktop().open(FileName);Open() throws an IOException and should be caught properly.Handling DirectoriesWhen we encounter a directory, which is the false case for isFile(), we have to display the contents in that directory. What we have to do here is a simple recursive call to the display function using this path after removing the all currently present components in the container.Container.removeAll() should do the trick.After adding the new buttons, it is necessary to refresh the panel. Remember that the newly added components will not be visible until you refresh the panel using revalidate() and repaint() functions present in the Panel class.container.revalidate(); container.repaint();Adding a back buttonIt is a basic requirement for File explorers to add back buttons. In order to do so, we have to remember the history of directories. A stack is used for this purpose. Whenever a directory is accessed, its parent is added to the stack. When the back button is pressed, the top of the stack is popped and that directory is displayed.Go to directoryAgain, the same display function LoadBase() is utilized here. LoadBase taked the full pathname of directory and when the user gives the directory path directly, all that we have to do is to pass the given text to LoadBase(). The path may be invalid and it is displayed using message dialog. isExist() function in the file class helps to check whether a file/directory exists.Loaded C Drive Using Go to to load D drive Suggested Read : Java Barcode Generator – Java Library Management Program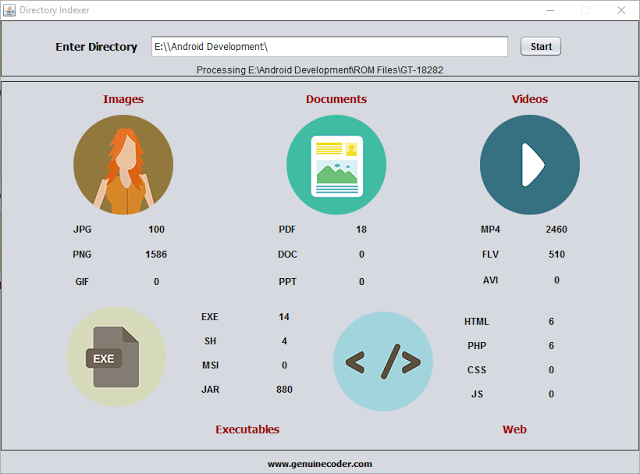
Directory / Folder Indexing Program Using Java
I thought it will be cool if I can make a program that scans some pen drive or hard disk connected to my PC in order find out how many images,videos or documents are there. In simple terms, a directory or folder/file indexing program. Thanks to java again.Directory Indexer Main Window Directory indexer uses the FILE class from java.io package. An object of FILE can store both files and directories. The parent or Root directory, from where we start indexing is read from the user using normal JTextField. Then a function called processDirectory() is called with argument as the given input text.The function, processDirectory() then create a new File with argument as given path. Then the list of files and directories present inside the directory are taken as a file array using listFiles() method from File class. If you are interested in finding more about file listing, read How tocreate a file explorer in java.File[] listFiles = fl.listFiles();After getting the list of contents in the given directory, a for loop is applied which will go through all the available contents (objects of File class). As we said earlier, it can be either a file or a directory. If it is a file, then we check its extension by splitting the name string using “.” Symbol. The fun thing about extension is, a file can contain more than 1 dotes. For example, I want to name my file as “genuine.coder.image.jpg”. It is perfectly alright to use this filename and if we go for splitting and taking the string after first dot, we will get “.coder” which is definitely not what we are expecting. So the solution is to find the string after last dot and it is achieved using the codeString[] extension = listFile.getName().split("[.]"); String ex = extension[extension.length - 1];So now we have the extension. All that we have to do is to check the string against the required extension (jpg,png,pdf etc) and increment the counter.if (ex.equalsIgnoreCase("jpg")) { jpg.setText(Integer.parseInt(jpg.getText()) + 1 + ""); }I found this way of incrementing the counter as a simple one (not efficient at all) since I don’t have to maintain some arrays for each separate extensions.If the file object which is being processed is not a file, then it may be a directory. If it is, then we have to get inside of that and index them also. A simple recursive call to the function will do the trick.if (listFile.isDirectory()) { processDirectory(listFile.getAbsolutePath()); //Recursive call to processDirectoy }I have used a thread to call the processDirectory() function. If I don’t, the updating on the UI (incrementing the counter) will be lagging. Using just one new thread, it is possible to achieve better refreshing and processing rates. For this purpose, a new class named directoryProcessor is created and implemented as Runnable which is then passed as a runnable object for new Thread object. The processDirectory is called from inside the run() method of directoryProcessor.Class directoryProcessorclass directoryProcessor implements Runnable { @Override public void run() { processDirectory(input.getText()); sts.setText("Completed"); JOptionPane.showMessageDialog(rootPane, "Indexing Completed", "Done", JOptionPane.INFORMATION_MESSAGE); } }Function processDirectory()public void processDirectory(String dir) { File fl = new File(dir); sts.setText("Processing " + dir); File[] listFiles = fl.listFiles(); for (File listFile : listFiles) { if (listFile.isFile()) { String[] extension = listFile.getName().split("[.]"); String ex = (extension[extension.length - 1]); if (ex.equalsIgnoreCase("jpg")) { jpg.setText(Integer.parseInt(jpg.getText()) + 1 + ""); } else if (ex.equalsIgnoreCase("png")) { png.setText(Integer.parseInt(png.getText()) + 1 + ""); } else if (ex.equalsIgnoreCase("gif")) { gif.setText(Integer.parseInt(gif.getText()) + 1 + ""); } else if (ex.equalsIgnoreCase("ppt")) { ppt.setText(Integer.parseInt(ppt.getText()) + 1 + ""); } else if (ex.equalsIgnoreCase("doc")) { doc.setText(Integer.parseInt(doc.getText()) + 1 + ""); } else if (ex.equalsIgnoreCase("pdf")) { pdf.setText(Integer.parseInt(pdf.getText()) + 1 + ""); } else if (ex.equalsIgnoreCase("mp4")) { mp4.setText(Integer.parseInt(mp4.getText()) + 1 + ""); } else if (ex.equalsIgnoreCase("flv")) { flv.setText(Integer.parseInt(flv.getText()) + 1 + ""); } else if (ex.equalsIgnoreCase("avi")) { avi.setText(Integer.parseInt(avi.getText()) + 1 + ""); } else if (ex.equalsIgnoreCase("exe")) { exe.setText(Integer.parseInt(exe.getText()) + 1 + ""); } else if (ex.equalsIgnoreCase("sh")) { sh.setText(Integer.parseInt(sh.getText()) + 1 + ""); } else if (ex.equalsIgnoreCase("jar")) { jar.setText(Integer.parseInt(jar.getText()) + 1 + ""); } else if (ex.equalsIgnoreCase("html")) { html.setText(Integer.parseInt(html.getText()) + 1 + ""); } else if (ex.equalsIgnoreCase("php")) { php.setText(Integer.parseInt(php.getText()) + 1 + ""); } else if (ex.equalsIgnoreCase("css")) { css.setText(Integer.parseInt(css.getText()) + 1 + ""); } else if (ex.equalsIgnoreCase("js")) { js.setText(Integer.parseInt(js.getText()) + 1 + ""); } } else if (listFile.isDirectory()) { try { processDirectory(listFile.getAbsolutePath()); } catch (Exception e) { System.err.println("Exception - " + e.getMessage()); } } } }
Install The Best Android Emulator For Ubuntu / Linux
When we consider android emulators, the first option is Google’s default Android Emulator available in the android-sdk. But on a normal computer (in my 4GB Ram, Core i3 3rd Gen Processor Laptop) it takes around 5 minute to boot and performance is very laggy. It becomes worse after starting android studio in case you are a developer. So I started looking for a faster yet stable android emulator for Linux. Genymotion
Genymotion is the best android emulr Linux versator I have used so far. It is fast, simple and can be integrated into android studio without any additional configuration. If you are looking for an android emulator for android development or just want to run WhatsApp or something on your computer, Genymotion is the right choice. Genymotion is free for personal use and can be downloaded from their site after signup. If you want to use Genymotion for business use, try Desktop Edition For Business. Requirements
Your system must have Virtualbox virtual machine present in order to use Genymotion. If you don’t have Virtualbox download the setup for your Linux version from Virtualbox linux installation page. Install it and restart system to continue.
How To Install Genymotion In Ubuntu / Linux
- Go to this Genymotion website and make a free account.
- Login using your account and go to this download Page
Download the right version of the setup for your computer (Select correct architecture 32bit or 64bit. If you are not sure, then download 32 bit ) - The downloaded file will be of .bin extension. Linux wont allow to run a file that is downloaded from internet. You have to give the file executable privilege to run it. To do so, open terminalEither copy and paste your file to home or change terminal working directory by using ‘cd’ command.Type chmod +x file-name.bin where file-name is the name the downloaded file
- Now, The installation will be in progress. Complete the installation
- After the installation, You can start Genymotion from your launcher/Menu. If it is not present, then start the program manually from /home/you-user name/genymotion/genymotion (You may have to make this program executable using chmod)
- Now you should see the following loading screen
- Once loaded, You should see a login prompt. For login, use your previous username and password.
- Now it is time to add a new phone to this emulator. You can do this by Clicking on the Add (+) button.
- You should see a list of available emulators here. There you can find devices with almost all android versions you have heard of. Choose any one you want and click on Next. In the new window, you can set a name for your device. Click Next.
- Wait for the downloading and installing complete. After you complete your virtual device installation, you will see the device in your Virtual Device List. Then you can add any number of emulators you want. In my case, I have added 3 of them.
- Congratulations. You have successfully added an emulator. Now it is time to run it. Select the available emulator and click on start button. Then a message box will appear saying “Initializing virtual device”
- It will take a little while to complete the firdt boot. Be patient :-). Here is a screenshot of my emulator
Keywords : Run android apps in linux, Run android apps in pc, Install Genymotion in linux ubuntu mint, Android emulator for linux, Fastest android emulator, Install apk in linux

How to Add Facebook Page Plugin to Your Website or Blog
Facebook is currently the best place to promote our websites. It is always a better idea to start a dedicated Facebook page for your blog or website. You will be astonished by the amount of traffic it can provide. Moreover, sharing links across social medias will help to build a sold set of backlinks, which are one of the important parameters for search engine rankings.As always, Let’s do this as steps.- Go to Facebook’s developer page by clicking here.

- Copy and paste your Facebook page address. My page address is facebook.com/thegenuinecoder. You can get this address by simply visiting the page and copy address from address bar.
It is possible to set Width and Height of the widget by giving required values in the proper text fields. But you can leave it empty if you want to.
- A live preview will be generated after you paste the URL. Now it is time to integrate this to website. Click on the ‘Get Code’ button.
- Copy The Step 2 Code. Paste it on your website, just below the <body> tag. [If you are using blogger, get HTML code from Template->Edit HTML option. Then Press ‘Save Template’]

- Now copy the code under Step 3 and place where you want this plugin to appear. [ In blogger, Add HTML/Java Script widget with this code ]. Save changes.
- Refresh your page. You will see a beautiful widget of your page. If you can’t, then carefully read and repeat the above steps.
Keywords : Add beautiful Facebook page plugin to your website.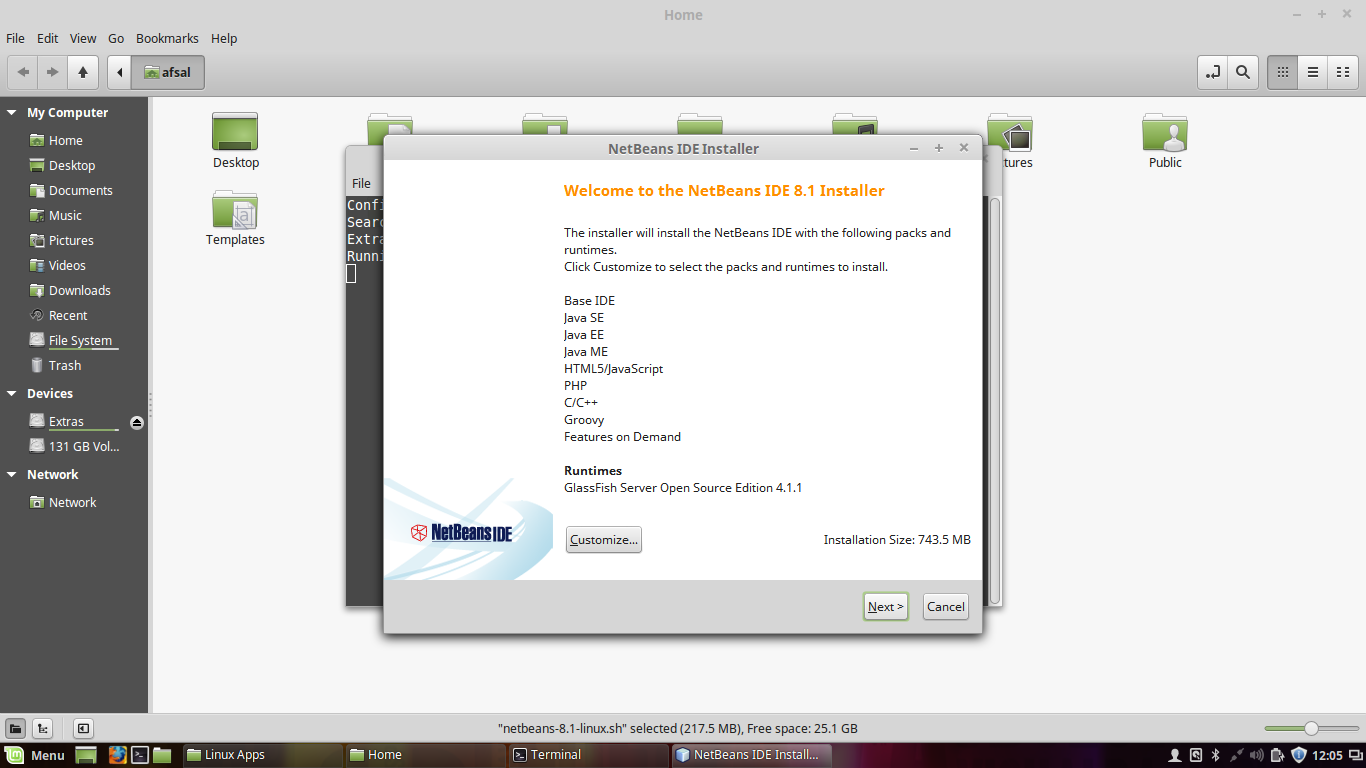
Install NetBeans with Oracle JDK in Ubuntu / Mint (Easy Way)
Programmers love to code in Linux. For me whether it is Android Studio or NetBeans, I used to get 2-3 times better speed in my Mint than in Windows. However, installing JDK offline in Linux is a tedious task. But NetBeans provides an easier way to do this. Let’s see how we can install Netbeans with Oracle JDK in linux.
Instead of installing the JDK, NetBeans only require an extracted JDK in the home directory. So let’s do it
-
- Download NetBeans executable for Linux (.sh File) and Oracle JDK(Download file like jdk-8uxx-linux-x64.tar.gz for x64 platform)
- Copy These downloaded files to Home Directory

- Extract The JDK in the Home folder itself

- Give the netbeans executable privilage using this command on terminal. Replace xx with your version.chmod +x netbeans-xxx.sh

- Now you can run the NetBeans setup using
./netbeans-xxx.sh

- The NetBeans setup will automatically detect the JDK from the HOME directory. You can proceed with the installer and finish it.

- Yeah ! You done it. Open NetBeans from your Launcher.
Keywords : How to install netbeans with jdk, Simple way to install netbeans in ubuntu or mint, oracle jdk install

How to set WhatsApp Profile Pic as Contact Picture
It is always nice to see the picture of our loved ones when they call us. But downloading their photos and then setting them as contact photo is a tedious job. What if we can simply set their WhatsApp photo as contact picture. Yeah! That seems to be a pretty good idea.
But… How?
Well, there is an App for that in google play store. Let me explain the process as steps.
- · Download Contact Photo Sync from here. Install it
- · Open it. You can see all your contacts in the app. The left side photo represents your current contact photo and right side one represents the photo available in WhatsApp. Remember, the right side photo will not be available until you save the person’s picture in WhatsApp manually.

Main Screen, Left side photo represents current contact photo and right side is the available whatsapp photo.
- · Select the contact which you want to update photo.
- · The application will ask for a confirmation to launch WhatsApp. Click OK.

Confirmation to launch whatsapp
- · This will launch WhatsApp profile of the person. Click on his/her profile pic and Save it (Share -> Save to gallery).
- · When you come back to the Contact Photo Sync App, you will be given another prompt to confirm the photo update.

Confirmation to set whatsapp image as profile pic - · Click YES, or YES, Not Show Again.
- · And yes! You are done.

All Done
- Search : Set WhatsApp profile pic as contact picture
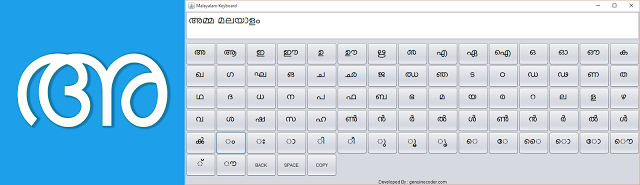
Malayalam Keyboard For PC ; Windows, Linux and Mac
Malayalam keyboard for PC / Desktop is an On-screen Malayalam keyboard that built using java programming language and will work on Windows, Linux and Mac operating systems.
Malayalam Keyboard for PC In the Unicode character representation Malayalam characters are available in between 0D00–0D7F hexadecimal values. In this software you can find all the Malayalam characters as buttons in the application. Clicking on the button will display corresponding character on the screen.Normally the Malayalam characters like ‘മ്മ’ is written using മ + ് + മ and ‘ക്ക‘’using ക + ് + ക. Ii this application, I have added a shortcut to this via Mouse Right Click. For example, the normal left click on the മ will give മ itself and right click on the മ will give മ്മ. This is applicable for all characters.The ‘BACK’ button will give the normal backspace effect and ‘SPACE’ will do the normal space. ‘SAVE’ can be used to copy the contents in textbox to memory/clipboard which then can be pasted to other applications.Malayalam Unicode tableSource Code:-package malayalamkeyboard;import java.awt.AWTException;import java.awt.Button;import java.awt.Font;import java.awt.FontFormatException;import java.awt.GraphicsEnvironment;import java.awt.Robot;import java.awt.Toolkit;import java.awt.datatransfer.Clipboard;import java.awt.datatransfer.StringSelection;import java.awt.event.ActionEvent;import java.awt.event.ActionListener;import java.awt.event.KeyEvent;import java.awt.event.MouseAdapter;import java.io.File;import java.io.IOException;import java.util.ArrayList;import java.util.logging.Level;import java.util.logging.Logger;import javax.swing.JButton;import javax.swing.JOptionPane;public class keyboard extends javax.swing.JFrame {ArrayList extrachars;ArrayList charStrings;ArrayList removable;String charSeq = “”;int ctrx = 0;Font customFont = null, customFontDisplay = null;public keyboard() {initComponents();loadExtraChars();try {//create the font to use. Specify the size!customFont = Font.createFont(Font.TRUETYPE_FONT, new File(“lib/font.ttf”)).deriveFont(25f);customFontDisplay = Font.createFont(Font.TRUETYPE_FONT, new File(“lib/font.ttf”)).deriveFont(30f);GraphicsEnvironment ge = GraphicsEnvironment.getLocalGraphicsEnvironment();//register the fontge.registerFont(Font.createFont(Font.TRUETYPE_FONT, new File(“lib/font.ttf”)));} catch (IOException e) {e.printStackTrace();} catch (FontFormatException e) {e.printStackTrace();}display.setFont(customFontDisplay);for (Object extrachar : extrachars) {char a = (char) extrachar;JButton btn = new JButton(a + “”);btn.setFont(display.getFont().deriveFont(display.getFont().getSize() + 5f));// btn.setFont(new java.awt.Font(“font”, 0, 34));btn.setFont(customFont);btn.setActionCommand(ctrx + “”);btn.addActionListener(new ActionListener() {@Overridepublic void actionPerformed(ActionEvent e) {display.setText(display.getText() + a);char[] chars = display.getText().toCharArray();}});btn.addMouseListener(new MouseAdapter() {public void mouseClicked(java.awt.event.MouseEvent evt) {if (evt.getButton() == 3) {char base = ‘u0d4d’;display.setText(display.getText() + a + base + a);}}});cntr.add(btn);ctrx++;}addExtraButttons();this.revalidate();this.repaint();this.setLocationRelativeTo(null);this.pack();}void loadExtraChars() {removable = new ArrayList<String>();removable.add(“d11”);removable.add(“d0d”);removable.add(“d04”);removable.add(“d3b”);removable.add(“d3c”);removable.add(“d45”);removable.add(“d49”);removable.add(“d4f”);removable.add(“d50”);removable.add(“d51”);removable.add(“d52”);removable.add(“d53”);removable.add(“d54”);removable.add(“d55”);removable.add(“d56”);removable.add(“d58”);removable.add(“d59”);removable.add(“d5a”);removable.add(“d5b”);removable.add(“d5c”);removable.add(“d5d”);removable.add(“d5e”);removable.add(“d5f”);removable.add(“d64”);removable.add(“d65”);removable.add(“d76”);removable.add(“d77”);removable.add(“d78”);removable.add(“d29”);removable.add(“d4e”);removable.add(“d3a”);removable.add(“d70”);removable.add(“d71”);removable.add(“d72”);removable.add(“d73”);removable.add(“d74”);removable.add(“d75”);removable.add(“d79”);removable.add(“d3d”);removable.add(“d44”);removable.add(“d62”);removable.add(“d63”);//Removing MALAYALAM NUMBERSremovable.add(“d66”);removable.add(“d67”);removable.add(“d68”);removable.add(“d69”);removable.add(“d6a”);removable.add(“d6b”);removable.add(“d6c”);removable.add(“d6d”);removable.add(“d6e”);removable.add(“d6f”);//Removed//Extras Spacingremovable.add(“d3e”);removable.add(“d3f”);removable.add(“d40”);removable.add(“d41”);removable.add(“d42”);removable.add(“d43”);removable.add(“d46”);removable.add(“d47”);removable.add(“d48”);removable.add(“d4a”);removable.add(“d4b”);removable.add(“d4c”);removable.add(“d4d”);removable.add(“d57”);//Extra Removablesremovable.add(“d60”);removable.add(“d61”);removable.add(“d7f”);removable.add(“d7f”);//extrachars = new ArrayList<Character>();charStrings = new ArrayList<String>();Character a = ‘u0D04’;for (int i = 0; i < 123; i++) {if (removable.contains(Integer.toHexString(a))) {a++;continue;}extrachars.add(a);a++;}extrachars.add((‘u0D7A’));extrachars.add((‘u0D7B’));extrachars.add((‘u0D7C’));extrachars.add((‘u0D7D’));extrachars.add((‘u0D7E’));extrachars.add((‘u0D7F’));extrachars.add((‘u0D02’));extrachars.add((‘u0D03’));extrachars.add((‘u0D3E’));extrachars.add((‘u0D3F’));extrachars.add((‘u0D40’));extrachars.add((‘u0D41’));extrachars.add((‘u0D42’));extrachars.add((‘u0D43’));extrachars.add((‘u0D46’));extrachars.add((‘u0D47’));extrachars.add((‘u0D48’));extrachars.add((‘u0D4A’));extrachars.add((‘u0D4B’));extrachars.add((‘u0D4C’));extrachars.add((‘u0D4D’));extrachars.add((‘u0D57’));}private void addExtraButttons() {JButton btn = new JButton(“BACK”);btn.addActionListener(new ActionListener() {@Overridepublic void actionPerformed(ActionEvent e) {try {display.requestFocus();Robot r = new Robot();r.keyPress(KeyEvent.VK_BACK_SPACE);r.keyRelease(KeyEvent.VK_BACK_SPACE);} catch (AWTException ex) {Logger.getLogger(keyboard.class.getName()).log(Level.SEVERE, null, ex);}}});cntr.add(btn);btn = new JButton(“SPACE”);btn.addActionListener(new ActionListener() {@Overridepublic void actionPerformed(ActionEvent e) {try {display.requestFocus();Robot r = new Robot();r.keyPress(KeyEvent.VK_SPACE);r.keyRelease(KeyEvent.VK_SPACE);} catch (AWTException ex) {Logger.getLogger(keyboard.class.getName()).log(Level.SEVERE, null, ex);}}});cntr.add(btn);btn = new JButton(“SAVE”);btn.addActionListener(new ActionListener() {@Overridepublic void actionPerformed(ActionEvent e) {Clipboard clpbrd = Toolkit.getDefaultToolkit().getSystemClipboard();clpbrd.setContents(new StringSelection(display.getText()), null);JOptionPane.showMessageDialog(rootPane, “Copied To Clipboard”);}});cntr.add(btn);}@SuppressWarnings(“unchecked”)// <editor-fold defaultstate=”collapsed” desc=”Generated Code”>//GEN-BEGIN:initComponentsprivate void initComponents() {cntr = new javax.swing.JPanel();jScrollPane1 = new javax.swing.JScrollPane();display = new javax.swing.JTextArea();jLabel1 = new javax.swing.JLabel();setDefaultCloseOperation(javax.swing.WindowConstants.EXIT_ON_CLOSE);setTitle(“Malayalam Keyboard”);cntr.setLayout(new java.awt.GridLayout(0, 15));display.setColumns(20);display.setLineWrap(true);display.setRows(1);jScrollPane1.setViewportView(display);jLabel1.setHorizontalAlignment(javax.swing.SwingConstants.CENTER);jLabel1.setText(“Developed By : genuinecoder.com”);javax.swing.GroupLayout layout = new javax.swing.GroupLayout(getContentPane());getContentPane().setLayout(layout);layout.setHorizontalGroup(layout.createParallelGroup(javax.swing.GroupLayout.Alignment.LEADING).addComponent(jScrollPane1, javax.swing.GroupLayout.DEFAULT_SIZE, 1213, Short.MAX_VALUE).addComponent(cntr, javax.swing.GroupLayout.DEFAULT_SIZE, javax.swing.GroupLayout.DEFAULT_SIZE, Short.MAX_VALUE).addComponent(jLabel1, javax.swing.GroupLayout.Alignment.TRAILING, javax.swing.GroupLayout.DEFAULT_SIZE, javax.swing.GroupLayout.DEFAULT_SIZE, Short.MAX_VALUE));layout.setVerticalGroup(layout.createParallelGroup(javax.swing.GroupLayout.Alignment.LEADING).addGroup(javax.swing.GroupLayout.Alignment.TRAILING, layout.createSequentialGroup().addComponent(jScrollPane1, javax.swing.GroupLayout.DEFAULT_SIZE, 78, Short.MAX_VALUE).addPreferredGap(javax.swing.LayoutStyle.ComponentPlacement.RELATED).addComponent(cntr, javax.swing.GroupLayout.DEFAULT_SIZE, 370, Short.MAX_VALUE).addGap(5, 5, 5).addComponent(jLabel1)));pack();}// </editor-fold>//GEN-END:initComponentspublic static void main(String args[]) {//<editor-fold defaultstate=”collapsed” desc=” Look and feel setting code (optional) “>/* If Nimbus (introduced in Java SE 6) is not available, stay with the default look and feel.* For details see http://download.oracle.com/javase/tutorial/uiswing/lookandfeel/plaf.html*/try {for (javax.swing.UIManager.LookAndFeelInfo info : javax.swing.UIManager.getInstalledLookAndFeels()) {if (“Nimbus”.equals(info.getName())) {javax.swing.UIManager.setLookAndFeel(info.getClassName());break;}}} catch (ClassNotFoundException ex) {java.util.logging.Logger.getLogger(keyboard.class.getName()).log(java.util.logging.Level.SEVERE, null, ex);} catch (InstantiationException ex) {java.util.logging.Logger.getLogger(keyboard.class.getName()).log(java.util.logging.Level.SEVERE, null, ex);} catch (IllegalAccessException ex) {java.util.logging.Logger.getLogger(keyboard.class.getName()).log(java.util.logging.Level.SEVERE, null, ex);} catch (javax.swing.UnsupportedLookAndFeelException ex) {java.util.logging.Logger.getLogger(keyboard.class.getName()).log(java.util.logging.Level.SEVERE, null, ex);}//</editor-fold>java.awt.EventQueue.invokeLater(new Runnable() {public void run() {new keyboard().setVisible(true);}});}// Variables declaration – do not modify//GEN-BEGIN:variablesprivate javax.swing.JPanel cntr;private javax.swing.JTextArea display;private javax.swing.JLabel jLabel1;private javax.swing.JScrollPane jScrollPane1;// End of variables declaration//GEN-END:variables}Keywords : Free malayalam keyboard for windows, Linux and Mac. Java Malayalam Keyboard, Malayalam keyboard program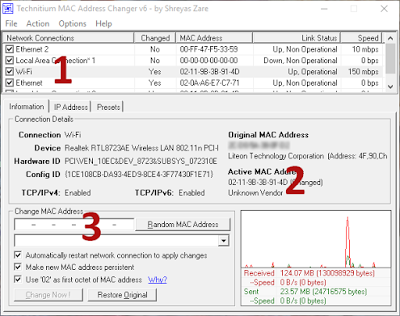
Easiest way to change Computer’s MAC Address in Windows
What is Actually the MAC Address?According to Wikipedia,
A media access control address (MAC address), also called physical address, is a unique identifier assigned to network interfaces for communications on the physical network segment. MAC addresses are used as a network addressfor most IEEE 802 network technologies, including Ethernet and Wi-Fi.Now, we want to change or mask our unique identity to something else. Technitium MAC Address Changer is an incredibly powerful yet easier tool to change MAC. Let us see how to change MAC address with just 3 clicks.Step 1:- Download Technitium MAC Address Changer from HEREStep 2:- Install and open itTechnitium MAC Address Changer Step 3: Select your currently connected network form the list ( Located as 1 in the image). You can easily identify the connection by looking into Link status. choose one with status as “Up, Operational”.Step 4: Identify your mac. You can check whether any other software has masked your MAC. If your original MAC and Active MAC are same, then it is not masked.Step 5: Click on the Random MAC Address ( Located as 3 in the figure ). Generate a random mac addressStep 6: Click on Change Now!After Click on the ‘Change Now’ You can see a prompt on successful MAC change.Step 7 : Well, There’s no step 7. Yet you can make sure your MAC is changed by looking into the Current MAC AddressMAC Address Changed If it is not your original MAC Address, Then you’re done.Keywords :Change MAC address easily in Windows, Change MAC Address in windows, How to change MAC Address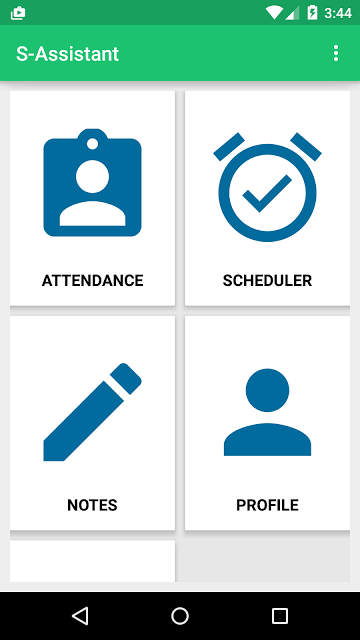
Android App for Teachers with Source Code
In this post, I am going to introduce an android application for teachers. Android is the ideal platform for developing such an application due to the wide variety of devices it supports. This Android app for teachers support basic functionalities such as adding student to each class/department, save notes, make schedules for classes etc. It also provides a CGPA (Cumulative Grade Point Average) calculator that basically calculate grade point average from the given grade points.
The First Activity Contains a Grid view that provides the connection to basic activities. The Attendance module is added to take attendance and store it in a database. The scheduler is basically used to schedule a particular event so that teachers won’t be needing another application as reminder.
Notes provides an easier way to save notes easily and quickly. Notes can also be associated with a subject so that it will be popped up when the teacher takes attendance for that subject.
Profile Module provides support to view and edit student data, along with activity to add new students.
Features Available
- Take attendance and keep them class wise
- Add New student. View each student’s attendance separately
- Edit Student/Attendance later
- Save notes subject wise
- Automatic notification about notes available when the teacher takes attendance
- Schedule classes
- CGPA calculator
- Simple and Material designed interface
Database DesignSimple sqlite database is used to store data through different tables.
import android.app.Activity; import android.database.Cursor; import android.database.sqlite.SQLiteDatabase; import android.util.Log; import android.widget.Toast; public class databaseHandler { SQLiteDatabase database; Activity activity; public databaseHandler(Activity activity) { this.activity = activity; database = activity.openOrCreateDatabase("ASSIST", activity.MODE_PRIVATE, null); createTable(); } public void createTable() { try { String qu = "CREATE TABLE IF NOT EXISTS STUDENT(name varchar(1000)," + "cl varchar(100), " + "regno varchar(100) primary key, contact varchar(100),roll integer);"; database.execSQL(qu); }catch (Exception e) { Toast.makeText(activity,"Error Occured for create table",Toast.LENGTH_LONG).show(); } try { String qu = "CREATE TABLE IF NOT EXISTS ATTENDANCE(datex date," + "hour int, " + "register varchar(100) ,isPresent boolean);"; database.execSQL(qu); }catch (Exception e) { Toast.makeText(activity,"Error Occured for create table",Toast.LENGTH_LONG).show(); } try { String qu = "CREATE TABLE IF NOT EXISTS NOTES(title varchar(100) not null," + "body varchar(10000), cls varchar(1000), sub varchar(1000) ,datex TIMESTAMP default CURRENT_TIMESTAMP);"; database.execSQL(qu); }catch (Exception e) { Toast.makeText(activity,"Error Occured for create table",Toast.LENGTH_LONG).show(); } try { String qu = "CREATE TABLE IF NOT EXISTS SCHEDULE(cl varchar(100),subject varchar(1000)," + "timex time, day_week varchar(100));"; database.execSQL(qu); }catch (Exception e) { Toast.makeText(activity,"Error Occured for create table",Toast.LENGTH_LONG).show(); } } public boolean execAction(String qu) { Log.i("databaseHandler", qu); try { database.execSQL(qu); }catch (Exception e) { Log.e("databaseHandler", qu); Toast.makeText(activity,"Error Occured for execAction",Toast.LENGTH_LONG).show(); return false; } return true; } Cursor execQuery(String qu) { try { return database.rawQuery(qu,null); }catch (Exception e) { Log.e("databaseHandler", qu); Toast.makeText(activity,"Error Occured for execAction",Toast.LENGTH_LONG).show(); } return null; } }database = activity.openOrCreateDatabase("ASSIST", activity.MODE_PRIVATE, null);The code is used to create or open the database in private mode. After opening the mysqli database all normal mysql operations can be performed on the database.
I always prefer executing custom sql queries. So I have made 2 functions called execQuery and execAction. The execAction uses execSql function to execute INSERT, DELETE OR UPDATE operations on the database. execAction returns a cursor which can be used to get the rows returned from SELECT query.Main Activity
As denoted earlier, the first activity contains Android Grid Layout which helps the user to easily find the content they are looking for. The following code is the layout XML for AppBase Activity.<?xml version="1.0" encoding="utf-8"?> <LinearLayout xmlns:android="http://schemas.android.com/apk/res/android" android:orientation="vertical" android:layout_width="match_parent" android:layout_height="match_parent" android:padding="10dp" > <GridView android:layout_width="match_parent" android:numColumns="2" android:id="@+id/grid" android:background="#e7e7e7" android:columnWidth="150dp" android:gravity="center" android:verticalSpacing="10dp" android:horizontalSpacing="10dp" android:stretchMode="columnWidth" android:layout_height="match_parent"> </GridView> </ LinearLayout >The Grid Layout has both width and height and Match Parent so that it will fit into the whole screen.
BaseActivity.java
Now let’s understand the code for the first activity.
import android.app.Activity; import android.content.Intent; import android.database.Cursor; import android.database.sqlite.SQLiteDatabase; import android.support.design.widget.FloatingActionButton; import android.support.design.widget.Snackbar; import android.support.v7.app.AppCompatActivity; import android.os.Bundle; import android.util.Log; import android.view.Menu; import android.view.MenuInflater; import android.view.MenuItem; import android.view.View; import android.widget.Button; import android.widget.EditText; import android.widget.GridView; import java.util.ArrayList; public class AppBase extends AppCompatActivity { private ArrayList<String> basicFields; private gridAdapter adapter; public static ArrayList<String> divisions ; private GridView gridView; public static databaseHandler handler; public static Activity activity; @Override public boolean onCreateOptionsMenu(Menu menu) { super.onCreateOptionsMenu(menu); MenuInflater inflater = getMenuInflater(); inflater.inflate(R.menu.mai_menu, menu); return true; } @Override protected void onCreate(Bundle savedInstanceState) { super.onCreate(savedInstanceState); setContentView(R.layout.base_layout); basicFields = new ArrayList<>(); handler = new databaseHandler(this); activity = this; getSupportActionBar().show(); divisions = new ArrayList(); divisions.add("S1 COMPUTER SCIENCE"); divisions.add("S2 COMPUTER SCIENCE"); divisions.add("S3 COMPUTER SCIENCE"); divisions.add("S4 COMPUTER SCIENCE"); divisions.add("S5 COMPUTER SCIENCE"); divisions.add("S6 COMPUTER SCIENCE"); divisions.add("S7 COMPUTER SCIENCE"); gridView = (GridView)findViewById(R.id.grid); basicFields.add("ATTENDANCE"); basicFields.add("SCHEDULER"); basicFields.add("NOTES"); basicFields.add("PROFILE"); basicFields.add("CGPA CALCULATOR"); adapter = new gridAdapter(this,basicFields); gridView.setAdapter(adapter); } public void loadSettings(MenuItem item) { Intent launchIntent = new Intent(this,SettingsActivity.class); startActivity(launchIntent); } public void loadAbout(MenuItem item) { Intent launchIntent = new Intent(this,About.class); startActivity(launchIntent); } }From the onCreate() method, we have inflated the xml layout. The database handler is defined as a public static variable so that it can be accessed from all other activities without the need of declaration and initialization. I have used a custom adapter for the grid view called gridAdapter.
adapter = new gridAdapter(this,basicFields);The gridAdapter should get the images and list of title to show the grid view. Here, I have passed the ArrayList basicFields as header and the images are loaded from the adapter itself.gridView.setAdapter(adapter);This will set the adapter as the adapter for grid view. Now Let’s consider the Custom Grid Adaptor for handling Grid view.Custom Grid Adapter
import android.app.Activity; import android.app.AlertDialog; import android.app.Dialog; import android.app.DialogFragment; import android.app.FragmentManager; import android.app.Notification; import android.app.NotificationManager; import android.app.PendingIntent; import android.content.DialogInterface; import android.content.Intent; import android.content.SharedPreferences; import android.database.Cursor; import android.net.Uri; import android.os.Bundle; import android.preference.PreferenceManager; import android.provider.Settings; import android.support.v4.app.NotificationCompat; import android.util.Log; import android.view.LayoutInflater; import android.view.View; import android.view.ViewGroup; import android.view.animation.Animation; import android.view.animation.ScaleAnimation; import android.widget.ArrayAdapter; import android.widget.BaseAdapter; import android.widget.DatePicker; import android.widget.EditText; import android.widget.ImageView; import android.widget.Spinner; import android.widget.TextView; import android.widget.Toast; import java.util.ArrayList; import java.util.StringTokenizer; public class GridAdapter extends BaseAdapter{ private ArrayList<String> names; public static Activity activity; public gridAdapter(Activity activity, ArrayList names) { this.activity = activity; this.names = names; } @Override public int getCount() { return names.size(); } @Override public Object getItem(int position) { return names.get(position); } @Override public long getItemId(int position) { return position; } @Override public View getView(int position, View v, ViewGroup parent) { if (v == null) { LayoutInflater vi = LayoutInflater.from(activity); v = vi.inflate(R.layout.grid_layout, null); } TextView textView = (TextView)v.findViewById(R.id.namePlacer); ImageView imageView = (ImageView)v.findViewById(R.id.imageHolder); if(names.get(position).toString().equals("ATTENDANCE")) { imageView.setImageResource(R.drawable.ic_attendance); v.setOnClickListener(new View.OnClickListener() { @Override public void onClick(View v) { FragmentManager fm = activity.getFragmentManager(); createRequest request = new createRequest(); request.show(fm,"Select"); } }); }else if(names.get(position).toString().equals("SCHEDULER")) { imageView.setImageResource(R.drawable.ic_schedule); v.setOnClickListener(new View.OnClickListener() { @Override public void onClick(View v) { Intent launchinIntent = new Intent(activity, scheduler.class); activity.startActivity(launchinIntent); } }); }else if(names.get(position).toString().equals("NOTES")) { imageView.setImageResource(R.drawable.ic_notes); v.setOnClickListener(new View.OnClickListener() { @Override public void onClick(View v) { Intent launchinIntent = new Intent(activity, noteActivity.class); activity.startActivity(launchinIntent); } }); }else if(names.get(position).toString().equals("PROFILE")) { imageView.setImageResource(R.drawable.ic_profile); v.setOnClickListener(new View.OnClickListener() { @Override public void onClick(View v) { Intent launchinIntent = new Intent(activity, profile_activity.class); activity.startActivity(launchinIntent); } }); } else if(names.get(position).toString().equals("CGPA CALCULATOR")) { imageView.setImageResource(R.drawable.ic_cgpa); v.setOnClickListener(new View.OnClickListener() { @Override public void onClick(View v) { Intent launchinIntent = new Intent(activity, cgpa_activity.class); activity.startActivity(launchinIntent); } }); } textView.setText(names.get(position).toString()); return v; } public static class createRequest extends DialogFragment { @Override public void onCreate(Bundle savedInstanceState) { super.onCreate(savedInstanceState); } @Override public Dialog onCreateDialog(Bundle savedInstanceState) { AlertDialog.Builder builder = new AlertDialog.Builder(getActivity()); // Get the layout inflater LayoutInflater inflater = getActivity().getLayoutInflater(); final View v = inflater.inflate(R.layout.pick_period, null); final DatePicker datePicker = (DatePicker) v.findViewById(R.id.datePicker); final EditText hour = (EditText)v.findViewById(R.id.periodID); final Spinner spn = (Spinner) v.findViewById(R.id.spinnerSubject); String qu = "SELECT DISTINCT sub FROM NOTES"; ArrayList<String> subs = new ArrayList<>(); subs.add("Not Specified"); Cursor cr = AppBase.handler.execQuery(qu); if(cr!=null) { cr.moveToFirst(); while(!cr.isAfterLast()) { subs.add(cr.getString(0)); Log.d("gridAdapter.class", "Cached " + cr.getString(0)); cr.moveToNext(); } }else Log.d("gridAdapter.class", "No SUBS" + cr.getString(0)); ArrayAdapter<String> adapterSpinner = new ArrayAdapter<String>(activity, android.R.layout.simple_spinner_dropdown_item, subs); assert spn != null; spn.setAdapter(adapterSpinner); builder.setView(v) // Add action buttons .setPositiveButton("Enter", new DialogInterface.OnClickListener() { @Override public void onClick(DialogInterface dialog, int id) { int day = datePicker.getDayOfMonth(); int month = datePicker.getMonth() + 1; int year = datePicker.getYear(); String date = year + "-" + month + "-" + day; String subject = spn.getSelectedItem().toString(); String qx = "SELECT title FROM NOTES where sub = '" + subject + "'"; Cursor cr = AppBase.handler.execQuery(qx); String subnames = ""; if(cr!=null) { cr.moveToFirst(); while(!cr.isAfterLast()) { subnames += (cr.getString(0)) + "n"; cr.moveToNext(); } } makeNotification(subnames); Cursor cursor = AppBase.handler.execQuery("SELECT * FROM ATTENDANCE WHERE datex = '" + date +"' AND hour = " + hour.getText() + ";"); if(cursor==null||cursor.getCount()==0) { Intent launchinIntent = new Intent(AppBase.activity, attendanceActivity.class); launchinIntent.putExtra("DATE", date); launchinIntent.putExtra("PERIOD", hour.getText().toString()); AppBase.activity.startActivity(launchinIntent); }else { Toast.makeText(getActivity(),"Period Already Added",Toast.LENGTH_LONG).show(); } } }) .setNegativeButton("Cancel", new DialogInterface.OnClickListener() { public void onClick(DialogInterface dialog, int id) { dialog.dismiss(); } }); return builder.create(); } } public static void makeNotification(String userIntrouble) { Log.d("NOTIFICATION","Building.........."); Intent notificationIntent = new Intent(activity.getApplicationContext(), noteActivity.class); PendingIntent pIntent = PendingIntent.getActivity(activity, 0, notificationIntent, 0); SharedPreferences sharedPrefs = PreferenceManager.getDefaultSharedPreferences(activity.getBaseContext()); Uri ring = Uri.parse(sharedPrefs.getString("Notification_Sound", Settings.System.DEFAULT_RINGTONE_URI.toString())); NotificationCompat.Builder builder = new NotificationCompat.Builder(activity.getBaseContext()) .setTicker("Ticker Title").setContentTitle("Notes Are Available For this subject") .setSmallIcon(R.drawable.ic_notes) .setStyle(new NotificationCompat.BigTextStyle().bigText(userIntrouble)) .setContentIntent(pIntent) .setSound(ring); Notification noti = builder.build(); noti.contentIntent = pIntent; noti.flags = Notification.FLAG_AUTO_CANCEL; NotificationManager notificationManager = (NotificationManager) activity.getSystemService(activity.NOTIFICATION_SERVICE); notificationManager.notify(0, noti); } }The custom adapter GridAdapter extends Android’s BaseAdapter and implements its methods. In the getView method, we have inflated both the title and ImageView using an if-else case.
Attendance Activity Create Dialog

Select Date for Registering Attendance Create request dialog is created when the user clicks on Attendance view in the Grid Layout. An onClickListener is added for the view v in the above code.
The dialog takes the date and hour(period) along with subject which is to be taken by the teacher. A notification module is added which will notify the teacher about the notes available for that particular subject once they click on the Enter option. Moreover clicking the Enter will launch new Activity called AttendanceActivity.
Intent launchinIntent = new Intent(AppBase.activity, attendanceActivity.class); launchinIntent.putExtra("DATE", date); launchinIntent.putExtra("PERIOD", hour.getText().toString()); AppBase.activity.startActivity(launchinIntent);In order to start the attendance activity, DATE and PERIOD data is passed through the intent. It is then accessed from the second activity and processed.Settings Activity
Setting activity provides option to clear application data. It wipes all the data from the database once selected.
The following data can be cleared.
- Schedule created
- Attendance data
- Notes saved
- Student Info

Setting Activity pref_general.xml
<PreferenceScreen xmlns:android="http://schemas.android.com/apk/res/android"> <Preference android:title="Clear Schedule data" android:summary="Clear all schedules" android:key="clear_schedule"/> <Preference android:title="Clear Attendance data" android:summary="Clear all Attendance Data" android:key="clear_attendance"/> <Preference android:title="Clear Notes data" android:summary="Clear all Notes Data" android:key="clear_notes"/> <Preference android:title="Clear Student data" android:summary="Clear all Student Data" android:key="clear_student"/> </PreferenceScreen>In the settings, I have added options to clear all the databases. The above code is the XML layout for the preferences. The xml is inflated by SettingsActivity.java usingaddPreferencesFromResource(R.xml.pref_general)Then for each preference entry event handler is provided using the code.
Preference myPref = findPreference("clear_schedule"); myPref.setOnPreferenceClickListener(new Preference.OnPreferenceClickListener() { public boolean onPreferenceClick(Preference preference) { //DO ACTION HERE }That’s all about the first activity of S-Assistant from Android app for teachers. There are many other modules in the program. I feel it is not a good idea to explain them all. Get the project source code from the following link.
Screenshots:-

Add New Student to database 
Create new note 
List of notes 
“Make New Schedule” Activity 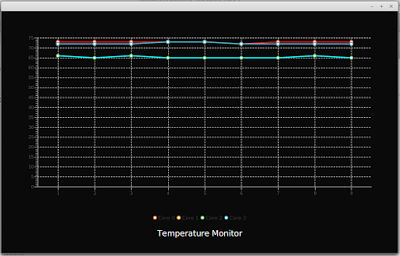
Temperature Monitor Prorgam using JavaFX
Today i am going to show you how to create a system temperature monitor program in JavaFX. This program use Line Chart from JavaFX library. In order to get the temperature readings, i have given a connection to the system terminal so that i can execute terminal commands within the Java program itself.Process proc = Runtime.getRuntime().exec("sensors"); BufferedReader reader = new BufferedReader(new InputStreamReader(proc.getInputStream()));This code will create a new process and will attach to the ‘sensors’ command. This program will work only on linux and the number of temperature readings will change from system to system. Using the process’s input stream we can read the output of the command passed through a Buffered Reader.After the establishment of connection with sensors, I have added an infinite loop with 1000ms sleep so that the temperature information will be updated each second. The returned data from process is taken and matched with a pattern [+]…. which will help to select the required temperature information alone. For this purpose, i have made use of Matcher and Pattern class in standard Java Library.If you are not familiar with JavaFX line graphs, i recommend reading this article How to Add JavaFX Charts / Graphs Tutorial.The processed data is then associated with 4 streams of XYData.Series() data structure to represent 4 different lines on the graph. Extensive CSS styling is used in this program to illustrate the capability of CSS to improve the look and feel of program (if it did :-)). The animations that can be seen on the video is the primitive animation associated with JavaFX LineChart.Watch the development in Action. Subscribe for more programs and tutorials
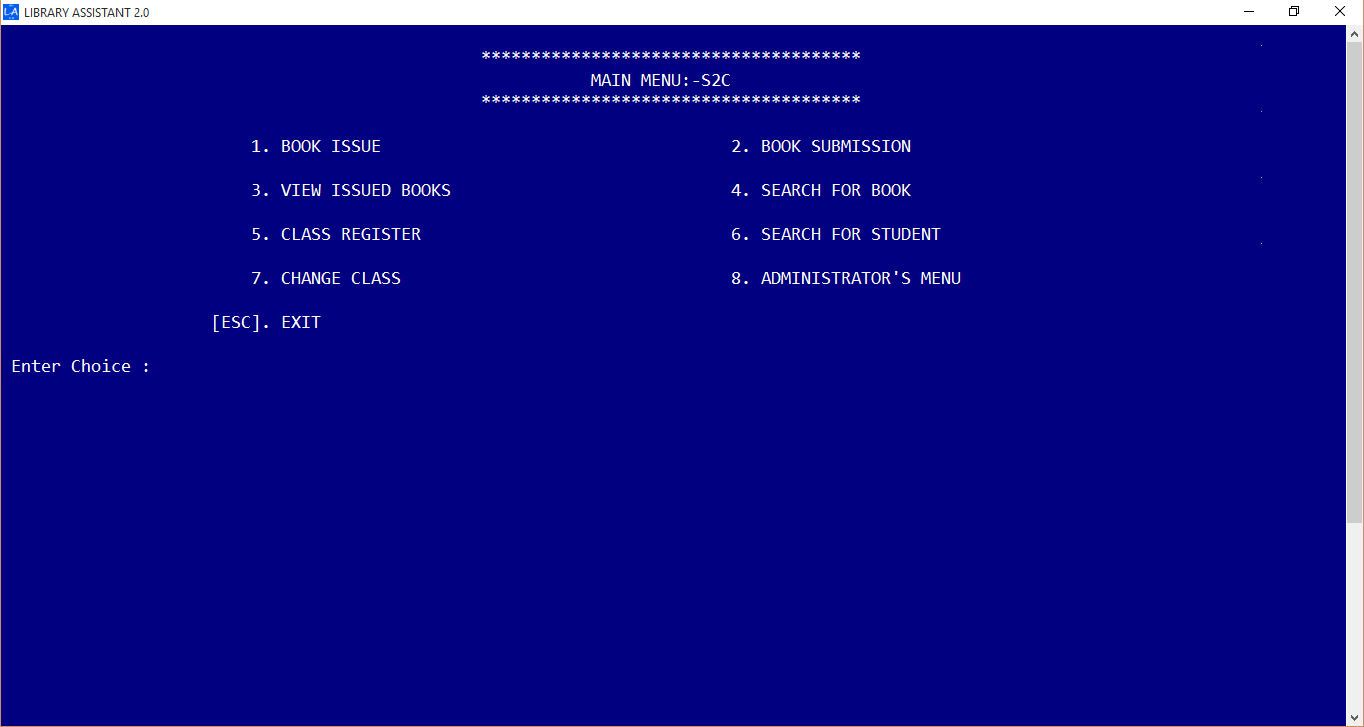
C++ Library Management Software with Source Code
Believe me, building a library management software in C++ is always a difficult thing. I have done library management software in java, c# and felt so much easiness in getting things done. Yet, this was my first library management software. Here I am going to share a simple library management program in C++ / Cpp as console application for schools and colleges. This program took me around 4 months to complete. The code is written as simple as possible. During the initial stage there were only just book issue and book submission modules. Later i have added more and more functions to improve Library Assistant. Thanks to Object Oriented Programming.Features
Simple and easy User Interface

Dasboard Ability to add and edit students, books

Add New Student Window Dedicated Admin Panel

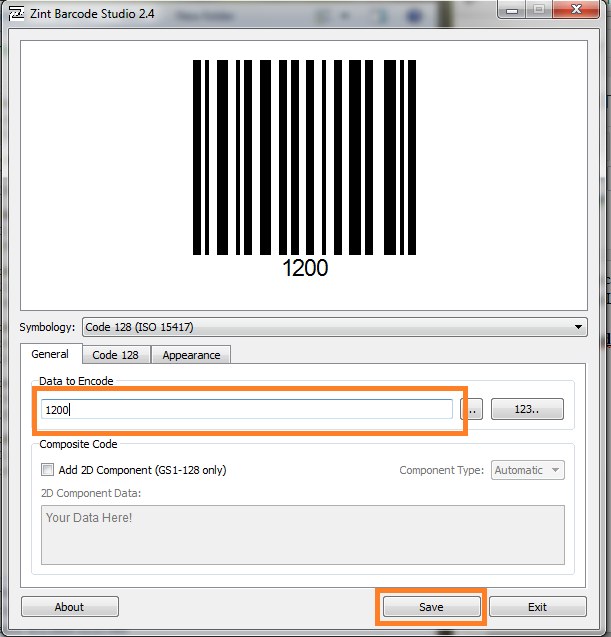
Admin Panel Barcode Reader Support
Bar code is supported for book issue and book submission process.
Organize Members by their Class / Level

Member Organization Library Overview Panel on Startup

Library Overview Multithreaded book and member search

Multithreaded Book Search Single-click Book Submission

Easy to use book submission The source code is developed using Visual Studio 2010.
How to run the program ?
- Download the zip file from above link
- Run Library Management System.exe
- The default password is ‘PPM’ (case sensitive).
- Done !
Read About Java Implementation of Library Software; Library Assistant 4
Keywords : Library Management system c++ – Library Management software c++

Library Assistant 4.0 – The Best Library Management Software For Free
Library Assistant is a free Java based simple library management software developed mainly for schools and colleges. Library Assistant 4.0 comes with great features such as enhanced search, bar code support etc.
Simple User Interface
LA is designed for simplicity by hiding complex things from the user. You can issue a book by just 3 clicks or submit a book with just 2 clicks!
BarCode Ready
Library Assistant supports barcode readers. You can increase your library efficiency simply by making use of Bar code readers with LA.
Run it Anywhere and Everywhere
LA is platform independent. You can run it on your favorite Operating System. All that you need is the Java Runtime Environment installed.
A username and password is required for logging in. You can set your username and password during initial configuration.
Advanced Book Search
You can search for a book by its Title, Author, Publisher, Book ID (Bar code Number) or even with its location on the library.LA introducing a new email notification feature that send a notification email to the members with details regarding book issue and fine amount.Track Members
Library Assistant can keep of track of member’s each activity. So you can easily differentiate between active and inactive members.
Have an idea ? Let me know
LA has been getting updated for last 3 years. If you want a particular feature to be added on to LA, let me know in the comments.
Before downloading library assistant, your computer must have the Java Runtime Environment (JRE) installed. If it is not installed, please download the latest version from the below link.
UNIX Shell Programming : grep,sed and awk
grep:-Operation, grep Family, Searching for File Content.sed:-Scripts, Operation, Addresses, commands, Applications, grep and sed.
awk:-Execution, Fields and Records, Scripts, Operations, Patterns, Actions, Associative Arrays, String Functions, Mathematical Functions, User Defined Functions, Using System commands in awk, Applications of awk, grep and sedgrep
grep stands for global regular expression print. It is a family of programs that is used to search the input file for all lines that match a specified regular expression and write them to the standard output file (monitor).Operation
To write scripts that operate correctly, we must understand how the greputilities work. For each line in the standard input (input file or keyboard), grep performs the following operations:1. Copies the next input line into the pattern space. The pattern space is a buffer that can hold only one text line.2. Applies the regular expression to the pattern space.3. If there is a match, the line is copied from the pattern space to the standard output.The grep utilities repeat these three operations on each line in the input.grep Flowchart
A flowchart for the grep utility is given on the left and two points are to be noted along with that. First, the flowchart assumes that no options were specified. Selecting one ore more options will change the flowchart. Second, although grepkeeps a current line counter so that it always knows which line is being processed, the current line number is not reflected in the flowchart.grep Operation ExampleLet’s take a simple example. We have a file having four lines. Our aim is to display any line in the file that contains UNIX. There are only three lines matching the grep expression. grephandles the following situations:1. grep is a search utility; it can search only for the existence of a line that matches a regular expression.2. The only action that grepcan perform on a line is to send it to standard output. If the line does not match the regular expression, it is not printed.3. The line selection is based only on the regular expression. The line number or other criteria cannot be used to select the line.4. grep is a filter. It can be used at the left- or right-hand side of a pipe.5. grep cannot be used to add, delete or change a line.6. grep cannot be used to print only part of a line.7. grep cannot read only part of a file.8. grep cannot select a line based on the contents of the previous or the next line. There is only one buffer, and it holds only the current line.The file contents are:Only one UNIXDOS only hereMac OS X is UNIXLinux is UNIX$ grep ‘UNIX’ file1grep Family
There are three utilities in the grep family: grep, egrep and fgrep. All three search one or more files and output lines that contain text that matches criteria specified as a regular expression. The whole line does not have to match the criteria; any matching text in the line is sufficient for it to be output. It examines each line in the file, one by one. When a line contains a matching pattern, the line is output. Although this is a powerful capability that quickly reduces a large amount of data to a meaningful set of information, it cannot be used to process only a portion of the data.fgrep (Fast grep): supports only string patterns, no regular expressions.grep: supports only a limited number of regular expressions.egrep (Extended grep): supports most regular expressions but not all of them.grep Family Options
There are several options available to the grep family. A summary is given below:OptionExplanation-b-c-i-l-n-s-v-x-f filePrecedes each line by the file block number in which it is foundPrints only a count of the number of lines matching the patternIgnores upper- / lowercase in matching text.Prints a list of files that contain at least one line matching the patternShows line number of each line before the line.Silent mode. Executes utility but suppresses all output.Inverse output. Prints lines that do not match pattern.Prints only lines that entirely match pattern.List of strings to be matched are in file.grep Family Expressions
As we have seen before, fast grep (fgrep) uses only sequence operators in a pattern; it does not support any of the other regular expression operators. Basic grep and extended grep (egrep) both accept regular expressions as shown in table below:AtomsgrepfgrepegrepOperatorsgrepfgrepegrepCharacterDotClassAnchorsBack Reference√√√√√√√√√^ $SequenceRepetitionAlternationGroupSave√All but ?√√√* ? +√√Expressions in the grep utilities can become quite complex, often combining several atoms and/or operators into one large expression. When operators and atoms are combined, they are generally enclosed in either single quotes or double quotes. Technically, the quotes are need only when there is a blank or other character that has a special meaning to the grep utilities. As a good technique, we should always use them.grep
The original of the file-matching utilities, grep handles most of the regular expressions. The middle road between the other two members of the family, grep allows regular expressions but is generally slower than egrep. It is the only member of the grepfamily that allows saving the results of a match for later use. In the example below, we use grep to find all the lines that end in the word the and then pipe the results to head and print the first five.students@firewall:~/test$ man bash > bash.txtstudents@firewall:~/test$ grep -n “the$” bash.txt | head -524: In addition to the single-character shell options documented in the46: shopt_option is one of the shell options accepted by the51: the standard output. If the invocation option is +O, the115: If arguments remain after option processing, and neither the -c nor the116: -s option has been supplied, the first argument is assumed to be theFast grep
If your search criteria require only sequence expressions, fast grep (fgrep) is the best utility. Because its expressions consist of only sequence operators, it is also easiest to use if you are searching for text characters that are the same as regular expression operators, such as the escape, parentheses or quotes. For example, to extract all lines of bash.txt that contain an apostrophe, we could use fgrepas shown below:students@firewall:~/test$ fgrep -n “‘” bash.txt | tail -55235: job spec is given, all processes in that job’s pipeline are5334: to mail that as well! Suggestions and `philosophical’ bug reports may5344: A short script or `recipe’ which exercises the bug5353: It’s too big and too slow.5362: Compound commands and command sequences of the form `a ; b ; c’ are notExtended grep
Extended grep (egrep) is the most powerful of the three grep utilities. While it doesn’t have the save option, it does allow more complex patterns. Consider the case where we want to extract all lines that start with a capital letter and end in letter ‘N’ (uppercase n). Our first attempt at this command is shown below:students@firewall:~/test$ egrep -n ‘^[A-Z].*N$’ bash.txt |head -514:DESCRIPTION126:INVOCATION1288:EXPANSION1748:REDIRECTION2060:ARITHMETIC EVALUATIONThis is relatively a complex expression. It has three parts. The first looks for any line that starts with an uppercase letter. The second part says it can be followed by any character zero or more times. The third part says such a matching line end with uppercase ‘N’.While the above expression is fine, we want to extend it such that we also want to find all lines that start with a space ‘ ‘ and end with the character comma ‘,’ and also end with period ‘.’. For doing this, we can use the alternation operator. We will design the pattern for each of the requirement and then combine the three patterns with alternation operator. The result is given below:students@firewall:~/test$ egrep -n ‘(^[A-Z].*N$)|(^ .*,$)|(^ .*.$)’ bash.txt|head -406 |tail -112058: recursive calls.2060:ARITHMETIC EVALUATION2064: for overflow, though division by 0 is trapped and flagged as an error.2068: order of decreasing precedence.2099: 0 when referenced by name without using the parameter expansion syntax.2104: to be used in an expression.2114: 35.2118: above.2126: the file argument to one of the primaries is one of /dev/stdin,2127: /dev/stdout, or /dev/stderr, file descriptor 0, 1, or 2, respectively,2128: is checked.Examples
1. Select the lines from the file that have exactly three characters.egrep ‘^…$’ testFile2. Select the lines from the file that have at least three characters.egrep ‘…’ testFile3. Select the lines from the file that have three or fewer charactersegrep –vn ‘….’ testFile4. Count the number of blank lines in the file.egrep –c ‘^$’ testFile5. Count the number of nonblank lines in the fileegrep –c ‘.’ testFile6. Select the lines from the file that have the string UNIXfgrep ‘UNIX’ testFile7. Select the lines from the file that have only the string UNIX.egrep ‘^UNIX$’ testFile8. Select the lines from the file that have the pattern UNIX at least two times.egrep ‘UNIX.*UNIX’ testFile9. Copy the file to the monitor but delete the blank lines.egrep –v ‘^$’ testFile10.Select the lines from the file that have at least two digits without any other characters in between.egrep ‘[0-9][0-9]’ testFile11.Select the lines from the file whose first nonblank character is A.egrep ‘^ *A’ testFile12.Select the lines from the file that do not start with A to G.egrep –n ‘^[^A-G]’ testFile13.Find out if John is currently logged into the system.who | grep ‘John’Searching for File Content
Some modern operating systems allow us to search for a file based on a phrase contained in it. This is especially handy when we have forgotten the filename but know that it contains a specific expression or set of words. Although UNIX doesn’t have this capability, we can use the grep family to accomplish the same thing.Search a Specific Directory
When we know the directory that contains the file, we can simply use grep by itself. For example, to find a list of all files in the current directory that contain “bash”, we should use the search as below. The option l prints out the filename of any file that has at least one line that matches the grepexpression.students@firewall:~/test$ lsbash.txt cmpFile1 fgLoop.scr file3 result.txtbiju.txt cmpFile2 file1 goodStudentscensusFixed dastardly.txt file2 myliststudents@firewall:~/test$ grep -l ‘bash’ *bash.txtbiju.txtfgLoop.scrSearch All Directories in a Path
When we don’t know where the file is located, we must use the find command with the execute criterion. The find command begins by executing the specified command, in this case a grep search, using each file in the current directory. It then moves through the subdirectories of the current file applying the grep command. After each directory, it processes its subdirectories until all directories have been processed.students@firewall:~/test$ find ~ -type f -exec grep -l “bash” {} ;/home/students/.bash_logout/home/students/passwd/home/students/test/fgLoop.scr/home/students/test/bash.txt/home/students/test/biju.txt/home/students/.profile/home/students/.bash_history/home/students/assg.txt/home/students/pd2.txt/home/students/sort.txt/home/students/.bashrcsed
sed is an acronym for stream editor. Although the name implies editing, it is not a true editor; it does not change anything in the original file. Rather sed scans the input file, line by line, and applies a list of instructions (called a sed script) to each line in the input file. The script, which is usually a separate file, can be included in the sed command line if it is a one-line command. The sed utility has three useful options. Option –n suppresses the automatic output. It allows us to write scripts in which we control the printing. Option –f indicates that there is a script file, which immediately follows on the command line. The third option –e is the default. It indicates that the script is on the command line, not in a file.Scripts
The sed utility is called like any other utility. In addition to input data, sed also requires one or more instructions that provide editing criteria. When there is only command, it may be entered from the keyboard. Most of the time, instructions are placed in a file known as a sed script (program). Each instruction in a sed script contains an address and a commandScript Formats
When the script fits in a few lines, its instructions can be included in the command line. The script must be enclosed in quotes. For longer scripts, or for scripts that are going to be executed repeatedly over time, a separate script file is preferred. The file is created with a text editor and saved. We may give an extension .sed to indicate that it is a sed script. Examples of both are given below:$ sed –e ‘address command’ input_file$ sed –f script.sed input_fileInstruction Format
Each instruction consists of an address and a command.address! (complement, optional)commandThe address selects the line to be processed (or not processed) by the command. The exclamation point (!) is an optional address complement. When it is not present, the address must exactly match a line to select the line. When the complement operator is present, any line that does not match the address is selected; line that match the address are skipped. The command indicates the action that sed is to apply to each input line that matches the address.Comments
A comment is a script line that documents or explains one or more instructions in a script. It is provided to assist the reader and is ignored by sed. Comment lines begin with a comment token, which the pound sign (#). If the comment requires more than one line, each line must start with the comment token.# This line is a comment2,14 s/A/B30d42dOperation
Each line in the input file is given a line number by sed. This number can be used to address lines in the text. For each line, sedperforms the following operations:1. Copies an input line to the pattern space. The pattern space is a special buffer capable of holding one or more text lines for processing.2. Applies all the instructions in the script, one by one, to all pattern space lines that match the specified addresses in the instruction.3. Copies the contents of the pattern space to the output file unless directed not to by the –n option flag.sed does not change the input file. All modified output is written to standard output and to be saved must be redirected to a file.When all of the commands have been processed, sed repeats the cycle starting with 1. When you examine this process carefully, you will note that there are two loops in this processing cycle. One loop processes all of the instruction against the current line. The second loop processes all lines.A second buffer, the hold space, is available to temporarily store one or more lines as directed by the sed instructions.To fully understand how sed interacts with the input file, let’s look at the example. The data file hello.dat contains the following text:Hello friendsHello guestsHello studentsWelcomeAnd the scripts file hello.sed contains the following lines:1,3s/Hello/Greetings/2,3s/friends/buddies/Now executing the command:$ sed –f hello.sed hello.datLet’s go through the different steps. Each line of the input file is copied over to the pattern space, and then all instructions are applied and then output.Addresses
The address in an instruction determines which lines in the input file are to be processed by the commands in the instruction. Addresses in sedcan be one of four types: single line, set of lines, range of lines and nested addresses.Single-Line Addresses
A single-line address specifies one and only one line in the input file. There are two single-line formats: a line number or a dollar sign ($), which specifies the last line in the input file. Examples are:4command16command$commandSet-of-Line Addresses
A set-of-line address is a regular expression that may match zero or more liens, not necessarily consecutive, in the input file. The regular expression is written between two slashes. Any line in the input file that matches the regular expression is processed by the instruction command. Two important points need to be noted: First, the regular expression may match several lines that may or may not be consecutive. Second, even if a line matches, the instruction may not find the data to be replaced. Examples are:/^A/command/B$/commandA special case of a set-of-line address is the every-line address. When the regular expression is missing, every line is selected. In other words, when there is no address, every line matches.Range Addresses
An address range defines a set of consecutive lines. Its format is start address, comma with no space, and end address:start-address,end-addressThe start and end address can be a sed line number or a regular expression as in the next example:line- number,line-numberline-number,/regexp//regexp/,line-number/regexp/,/regexp/When a line that is in the pattern space matches a start range, it is selected for processing. At this point, sed notes that the instruction is in a range. Each input line is processed by the instruction’s command until the stop address matches a line. The line that matches the stop address is also processed by the command, but at that point, the range is no longer active. If at some future line the start range again matches, the range is again active until a stop address is found. Two important points need to be noted: First, while a range is active, all other instructions are also checked to determine if any of them also match an address. Second, more than one range may be active at a time. Examples are given below:A———B—————C———-D————-B—————–C—————–A———–A—————–B———–C————-A——————C————-3,/^A//^A/,/^B/A special case of range address is 1,$, which defines every line from the first line (1) to the last line ($). However, this special case address is not the same as the set-of-lines special case address, which is not address. Given the following two addresses:1. command 2. 1,$commandsed interprets the first as a set-of-line address and the second as a range address. Some commands, such as insert (i) and append (a) can be used only with a set-of-line address. These commands accept no address but do not accept 1,$ addresses.Nested Addresses
A nested address is an address that is contained within another address. While the outer (first) address range, by definition, must be either a set of lines or an address range, the nested address may be either a single line, a set of lines or another range.Let’s look at two examples. In the first example, we want to delete all blank lines between lines 20 and 30. The first command specifies the line range: it is the outer command. The second command, which is enclosed in braces, contains the regular expression for a blank line. It contains the nested address.20,30{/^$/d}In the second example, we want to delete all lines that contain the work Raven, but oly if the line also contains the word Quoth. In this case, the outer address searches for lines containing Raven, while the inner address looks for lines containing Quoth. What is especially interesting about this example is that the outer address is not a block of lines but a set of lines spread throughout the file./Raven/{/Quoth/d}Commands
There are 25 commands that can be used in an instruction. They may be grouped into nine categories based on how they perform their task. They are Line Number commands, Modify commands, Substitute commands, Transform commands, Input/Output commands, Files commands, Branch commands, Hold space commands and Quit commands.Line Number Command
The Line number command (=) writes the current line number at the beginning of the line when it writes the line to the output without affecting the pattern space. It is similar to the grep –n option. The only difference is that the line number is written on a separate line. The following example shows the usage. Note that this example uses the special case of the set-of-line address – there is no address, so the command applies to every line.$ sed ‘=’ TheRavenV11Once upon a midnight dreary, while I pondered, weak and weary2Over many a quaint and curious volume of forgotten lore3While I nodded, nearly napping, suddenly there came a tapping4As of someone gently rapping, rapping at my chamber door.5“’Tis some visitor,” I muttered, “tapping at my chamber door6Only this and nothing more.”The next eample, we print only the line number of lines beginning with an upper-case O. To do this we must use the –n option.$ sed –n ‘/^O/=’ TheRavenV126Modify Commands
Modify commands are used to insert, append, change or delete one or more whole lines. The modify commands require that any text associated with them be placed on the next line in the script. Therefore, the script must be in a file; it cannot be coded on the shell command line. Also, the modify commands operate on the whole line. In other words, they are line replacement commands. This means that we can’t use these sedcommands to insert text into the middle of a line. Whatever text you supply will completely replace any lines that match the address.Insert Command (i)
Insert adds one or more lines directly to the output before the address. This command can only be used with the single line and a set of lines; it cannot be used with a range. In the next example, we insert a title at the beginning of Poe’s “The Raven”.$ sed –f insertTitle.sed TheRavenV1 | cat –n# Script Name: insertTitle.sed# Adds a title to file1iThe RavenByEdgar Allan Poe1: The Raven2: By3: Edgar Allan Poe4: Once upon a midnight dreary, …If you use the insert command with the all lines address, the lines are inserted before every line in the file. This is an easy way to quickly double space a file.$ sed –f insertBlankLines.sed TheRavenV1# Script Name: insertBlankLines.sed# This script inserts a blank line before all lines in a filei# End of scriptAppend Command (a)
Append is similar to the insert command except that it writes the text directly to the output after the specified line. Like insert, append cannot be used with a range address. Inserted and appended text never appear in sed’s pattern space. They are written to the output before the specified line (insert) or after the specified line (append), even if the pattern space is not itself written. Because they are not inserted into the pattern space, they cannot match a regular expression, nor do they affect sed’s internal line counter. The following example demonstrates the append command by appending a dashed line separator after every line and “The End” after the last line of “The Raven”.$ sed –f appendLineSep.sed TheRavenV1# Script Name: appendLineSep.sed# This script appends dashed dividers after each linea———————————$aThe EndChange Command (c)
Change replaces a matched line with new text. Unlike insert and append, it accepts all four address types. In the next example, we replace the second line of Poe’s classic with a common thought expressed by many a weary calculus student.$ sed –f change.sed TheRavenV1# Script Name: change.sed# Replace second line of The Raven2cOver many an obscure and meaningless problem of calculus boreDelete Patten Space Command (d)
The delete command comes in two versions. When a lowercase delete command (d) is used, it deletes the entire pattern space. Any script commands following the delete command that also pertain to the deleted text are ignored because the text is no longer in the pattern space.$ sed ‘/^O/d’ TheRavenV1Delete Only First Line Command (D)
When an uppercase delete command (D) is used, only the first line of the pattern space is deleted. Of course, if the only line in the pattern space, the effect is the same as the lowercase delete.Substitute Command (s)
Pattern substitution is one of the most powerful commands in sed. In general, substitute replaces text that is selected by a regular expression with a replacement string. Thus, it is similar to the search and replace found in text editors. With it, we can add, delete or change text in one or more lines.Addresss/pattern/Replacement String/Flag(s)Search Pattern
The sed search pattern uses only a subset of the regular expression atoms and patterns. The allowable atoms and operators are shown below.AtomsAllowedOperatorsAllowedCharacter√Sequence√Dot√Repetition* ? {…}Class√Alternation√Anchors^ $GroupBack Reference√Save√When a text line is selected, its text is matched to the pattern. If matching text is found, it is replaced by the replacement string. The pattern and replacement strings are separated by a triplet of identical delimiters, slashes (/) in the example given before. Any character can be used as the delimiters, although the slash is the most common.Pattern Matches Address
If the address contains a regular expression that is same as the pattern we want to match, that is a special case. Here, we don’t need to repeat the regular expression in the substitute command. We do need to show that it is omitted, however, by coding two slashes at the beginning of the pattern. An example is given below.$ sed ‘/love/s//adore/’ browning.txtInput:How do I love thee? Let me count the ways.I love thee to the depth and breadth and heightMy soul can reach, when feeling out of sightFor the ends of being and ideal grace.I love thee to the level of everyday’sMost quiet need, by sun and candle-light.Output:How do I adore thee? Let me count the ways.I adore thee to the depth and breadth and heightMy soul can reach, when feeling out of sightFor the ends of being and ideal grace.I adore thee to the level of everyday’sMost quiet need, by sun and candle-light.Replace String
The replacement text is a string. Only one atom and two meta-characters can be used in the replacement string. The allowed replacement atom is the back reference. The two meta-character tokens are the ampersand (&) and the back slash (). The ampersand is used to place the pattern in the replacement string; the backslash is used to escape an ampersand when it needs to be included in the substitute text (if it is not quoted, it will be replaced by the pattern). The following example shows how the meta-characters are used. In the first example, the replacement string becomes *** UNIX ***. In the second example, the replacement string is now & forever.$ sed ‘s/UNIX/*** & ***/’ file1$ sed ‘/now/s//now & forever/’ file1Substitute Operation
As we have seen before, when the pattern matches the text, sed first deletes the text and then inserts the replacement text. This means that we can use the substitute command to add, delete or replace part of a line.Delete Part of a Line: To delete part of a line, we leave the replacement text empty. In other words, partial line deletes are a special substitution case in which the replacement is null. The following example deletes all digits in the input from standard input.$ sed ‘s/[0-9]//g’Usually sed command operates only on the first occurrence of a pattern in a line. In the above example, we wanted to delete all digits. Therefore, we used the global flag (g) at the end of the pattern. If we did not use it, only the first digit on each line would be deleted.Change Part of a Line: To change only part of a line, we create a pattern that matches the part to be changed and then place the new text in the replacement expression. In the following example, we change every space in the file to a tab.$ sed ‘s/ / /g’Now is the timeFor all good studentsTo come to the aidof their college.Now is the timeFor all good studentsTo come to the aidof their college.Add to Part of a Line: To add text to a line requires both a pattern to locate the text and the text that is to be added. Because the pattern deletes the text, we must include it in the new text.The next example add two spaces at the beginning of each line and two dashes at the end of each line.$ sed –f addPart.sed#!/bin/ksh# Script Name: addPart.sed# Adds two spaces at the beginning of line and – to end of lines/^/ /s/$/–/Back References
The examples in the previous section were all very simple and straightforward. More often, we find that we must restore the data that we deleted in the search. This problem is solved with the regular expression tools as demonstrated. The sed utility uses two different back references in the substitution replacement string: whole pattern (&) and numbered buffer (d). The whole pattern substitutes the deleted text into the replacement string. In numbered buffer replacement, whenever a regular expression matches tex, the text is placed sequentially in one of the nine buffers. Numbered buffer replacement (d), in which the d is a number between 1 and 9, substitutes the numbered buffer contents in the replacement string.s/—–/—–&—–/s/(—–)…(—–)/——1——2/Whole Pattern Substitution: When a pattern substitution command matches text in the pattern space, the matched text is automatically saved in a buffer (&). We can then retrieve its contents and insert it anywhere, and as many times as needed, into the replacement string. Using the & buffer therefore allows us to match text, which automatically deletes it, and then restore it so that it is not lost. As an example, we can rewrite the previous example of adding two spaces at the beginning of line and two dashes at the end of the line with a single command.$ sed ‘s/^.*$/ &–/’Another example is to modify the price list of a restaurant menu so that the $ symbol is added before the prices.$ sed ‘s/[0-9]/$&/’ priceFileNumbered Buffer Substitution: Numbered buffer substitution uses one or more of the regular expression numbered buffers. We use it when the pattern matches part of the input text but not all of it. As an example, let’s write a script that reformats a social security number with dashes. We assume that all nine-digit numbers are social security numbers. There are three parts to a social security number: three digits-two digits-four digits. This problem requires that we find them and reformat them. Our script uses a search pattern that uses the numbered buffers to save three constitutive digits followed by two digits and then four digits. Once a complete match is found, the numbered buffers are used to reformat the numbers.$ sed ‘s/([0-9]{3})([0-9]{2})([0-9]{4})/1–2–3/’ empFileGeorge Washigton 001010001John Adams 002020002Thomas Jefferson 003030003James Madison 123456789George Washigton 001-01-0001John Adams 002-02-0002Thomas Jefferson 003-03-0003James Madison 123-45-6789Substitute FlagsThere are four flags that can be added at the end of the substitute command to modify its behaviour: global substitution (g), specific occurrence substitution (digit), print (p) and write file (w file-name).Global Flag
The substitute command only replaces the first occurrence of a pattern. If there are multiple occurrences, none after the first are changed.root@firewall:/var/log# sed ‘s/cat/dog/’Mary had a black cat and a white cat.Mary had a black dog and a white cat.root@firewall:/var/log# sed ‘s/cat/dog/g’Mary had a black cat and a white cat.Mary had a black dog and a white dog.Specific Occurrence Flag
We now know how to change the first occurrence and all o fthe occurrences of a text pattern. Specific occurrence substitution (digit) changes any single occurrence of text that matches the pattern. The digit indicates which one to change. To change the second occurrence of a pattern, we use 2; to change the fifth, we use 5.root@firewall:/var/log# sed ‘s/cat/dog/2’Mary had a black cat, a yetllow cat and a white cat.Mary had a black cat, a yetllow dog and a white cat.Print Flag
There are occasions when we do not want to print all of the output. For example, when developing a script, it helps to view only the lines that have been changed. To control the printing from within a script, we must first turn off the automatic printing. This is done with the –n option. Once the automatic printing has been turned off, we can add a print flag to the substitution command.-rw-r–r– 1 root root 170 Feb 13 10:12 Feb2013root@firewall:~# ls -l | sed -n “/^-/s/(-[^ ]*).*:..(.*)/12/p”-rw-r–r– Feb2013-rw-r–r– fileList-rw-r–r– ifconfig.txt-rw-r–r– iptables_1.lst-rw-r–r– iptables_2.lst-rw-r–r– iptables.lstWrite File Flag
The write file command is similar to the print flag. The only difference is that rather than a print command we use the write command. One caution: there can be only one space between the command and the filename. To write the files in the previous example to a file, we would change the code as shown below.Transform Command (y)
It is sometimes necessary to transform one set of characters to another. For example, IBM mainframe text file are written in a coding system known as EBCDIC. In EBCDIC, the binary codes for characters are different from ASCII. To read an EBCDIC file, therefore, all characters must be transformed to their ASCII equivalent as the file is read. The transform command (y) requires two parallel sets of characters. Each character in the first string represents a value to be changed to its corresponding character in the second string. Another example is to translate the lowercase vowels to the uppercase vowels below:root@firewall:~# sed ‘y/aeiou/AEIOU/’A good time was had by all Under the Harvest Moon last September.A gOOd tImE wAs hAd by All UndEr thE HArvEst MOOn lAst SEptEmbEr.Input and Output Commands
The sed utility automatically reads text from the input file and writes data to the output file, usually standard output. In this section, we discuss commands that allow us to control the input and output more fully. There are five input/output commands: next (n), append next (N), print (p), print first line (P) and list (l).Next Command (n)
The next command (n) forces sedto read the next text line from the input file. Before reading the next line, however, it copies the current contents of the pattern space to the output, deletes the current text in the pattern space, and then refills it with the next input line. After reading the input line, it continues processing through the script. The next example, we use the next command to force data to be read. Whenever a line that starts with a digit is immediately followed by a blank line, we delete the blank line.students@firewall:~/test$ cat deleteBlankLines.sed# Script Name: deleteBlankLines.sed# This cript deletes blank likes only if the preceding line starts with a number/^[0-9]/{n/^$/d}students@firewall:~/test$ sed -f deleteBlankLines.sed deleteBlankLines.datSecond Line: Line 1 & Line 3 blank4th line followed by non-blank lineThis is line 56th line followed by blank lineLast line (#8)Append Next Command (N)
Whereas the next command clears the pattern space before inputting the next line, the append nextcommand (N) does not. Rather, it adds the next input line to the current contents of the pattern space. This is especially useful when we need to apply patterns to two or more lines at the same time.To demonstrate the append next command, we create a script that appends the second line to the first, the fourth to the third and so on until the end of the file. Note however that if we simply append the lines, when they are printed they will revert to two separate lines because there is a newline at the end of the first line. After we append the lines, therefore, we search for the newline and replace it with a space. The file consists of lines filled with the line number.$ sed –f appendLines.sed appendLines.dat# Script Name: appendLines.sed# This script appends every two lines so that the output is Line Line2,# Line 3 Line4 etc.Ns/n/ /InputOutput11111one111111111122222two222222222233333three3333333344444four44444444455555five55555555511111one1111111111 22222two222222222233333three33333333 44444four44444444455555five555555555Another interesting and much useful example replaces multiple blank lines with only one.$ sed –f appendBlkLines.sed appendBlkLines.dat/^$/{$!N/^n$/D}The $!N command is interpreted as “if the line is not the last line”.Print Command (p)
The print command (p) copies the current contents of the pattern space to the standard output file. If there are multiple lines in the pattern space, they are all copied. The contents of the pattern space are not deleted by the print command.$ sed ‘p’ linesOfNums.dat111111111122222222223333333333111111111111111111112222222222222222222233333333333333333333Print First Line Command (P)
Whereas the print command prints the entire contents of the pattern space, the print first line command (P) prints only the first line. That is, it prints the contents of the pattern space up to and including a newline character. Any text following the first newline is not printed.To demonstrate the print first line, let’s write a script that prints a line only if it is followed by a line that begins with a tab. This problem requires that we first append two lines in the pattern space. We then search the pattern space for a newline immediately followed by a tab. If we find this combination, we print only the first line. We then delete the first line only.$ sed –nf printFirstLine.sed printFirstLine.dat# Script Name: printFirstLine.sed$!N/n /PDThis is line1.This is line2.Line 3 starts with a tab.Line 4 starts with a tab.This is line 5. It’s the last line.This is line2.Line 3 starts with a tab.List Command (l)
The list command (l) converts the unprintable characters to their octal code.File Commands
There are two file commands that can be used to read and write files. The basic format for read and write commands are shown below.addressr/wfile-nameExactly one spaceRead File Command ( r )
The read file command ( r) reads a file and places its contents in the output before moving to the next command. It is useful when you need to insert one or more common lines after text in a file. The contents of the file appear after the current line (pattern space) in the output. An example is to prepare a letter with a standard letter head and signature.$ sed –f readFile.sed readFile.dat# Script Name: readFile.sed1 r letterhead.dat$ r signature.datWrite File Command (w)
The write file command (w) writes (actually appends) the contents of the pattern space to a file. It is useful for saving selected data to a file. For example, let’s create an activity log in which entries are grouped by days of the week. The end of each day is identified by a blank line. The first group of entries represents Monday’s activity, the second group represents Tuesday and so forth. The first word in each activity line is the day of the week.$ sed –nf writeFile.sed aptFile.dat# Script Name: writeFile.sed/Monday/,/^$/w Monday.dat/Tuesday/,/^$/w Tuesday.dat/Wednesday/,/^$/w Wednesday.dat/Thursday/,/^$/w Thursday.dat/Friday/,/^$/w Friday.dat/Saturday/,/^$/w Saturday.dat/Sunday/,/^$/w Sunday.datBranch Commands
The branch commands change the regular flow of the commands in the script file. Recall that for every line in the file, sed runs through the script file applying commands that match the current pattern space text.. At the end of the script file, the text in the pattern space is copied to the output file, and the next text line is read into the pattern space replacing the old text. Occasionally we want to skip the application of the commands. The branch commands allow us to do just that, skip one or more commands in the script file.Branch Label
Each branch command must have a target, which is either a label or the last instruction in the script (a blank label). A label consists of a line that beings with a colon (:) and is followed by up to seven characters that constitute the label name. There can be no other commands or text on the script-label line other than the colon and the label name. The label name must immediately follow the colon; there can be no space between the colon and the name, and the name cannot have embedded spaces. An example of the label is::comHereBranch Command
The branch command (b) follows the normal instruction format consisting of an address, the command (b), and an attribute (target) that can be used to branch to the end of the script or to a specific location within the script. The target must be blank or match a script label in the script. If no label is provided, the branch is to be end of the script (after the last line), at which point the current contents of the pattern space are copied to the output file and the script is repeated for the next input line.The next example demonstrates the basic branch command. It prints lines in a file once, twice or three times depending on a print control at the beginning of the file.$ sed –f branch.sed branch.dat# Script Name: branch.sed# This script prints a line multiple times/(1)/ b/(2)/ b print2/(3)/ b print3# Branch to end of scriptb# print three:print3ppb# print two:print2pPrint me once.(2)Print me twice.(3)Print me thrice.(4)Print me once.Print me once.(2)Print me twice.(2)Print me twice.(3)Print me thrice.(3)Print me thrice.(3)Print me thrice.(4)Print me once.Branch on Substitution Command
Rather than branch unconditionally, we may need to branch only if a substitution has been made. In this case, we use the branch on substitution or as it is also known, the test command (t). Its format is same as the basic branch command.students@firewall:~/test$ sed -f branchSub.sed branchSub.dat# Script Name: branchSub.sed# This script prints a line multiple timess/(1)//ts/(2)//t print2s/(3)//t print3# Branch to end of scriptb# print three:print3ppb# print two:print2p(1)Print me once.(2)Print me twice.(3)Print me thrice.Default: print me once.Print me once.Print me twice.Print me twice.Print me thrice.Print me thrice.Print me thrice.Default: print me once.Hold Space Commands
The sed has actually a hold space which can be used for saving the pattern space. There are five commands that are used to move text back and forth between the pattern space and hold space: hold and destroy (h), hold and append (H), get and destroy (g), get and append (G) and exchange (x).Hold and Destroy Command
The hold and destroy command (h) copies the current contents of the pattern space to the hold space and destroys any text currently in the hold space.Hold and Append Command
The hold and append command (H) appends the current contents of the pattern space to the hold space.Get and Destroy Command
The get and destroy (g) copies the text in the hold space to the pattern space and destroys any text currently in the pattern space.Get and Append Command
The get and append command (G) appends the current contents of the hold space to the pattern space.Exchange Command
The exchange command (x) swaps the text in the pattern and hold spaces. That is the text in the pattern space is moved to the hold space and the data that were in the hold space are moved to the pattern space.Applications, grep and sed. awk:-Execution, Fields and Records, Scripts, Operations, Patterns, Actions, Associative Arrays, String Functions, Mathematical Functions, User Defined Functions, Using System commands in awk, Applications of awk, grep and sed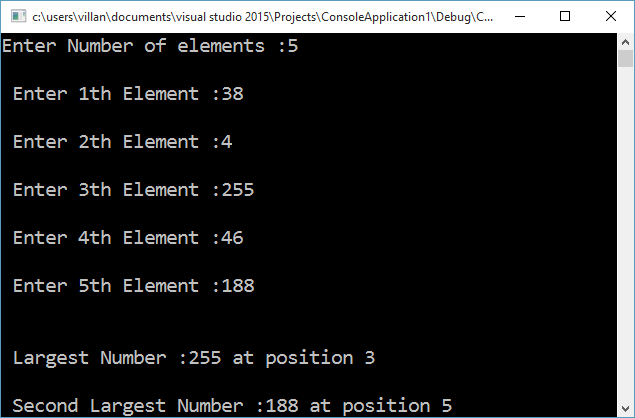
C++ program to find the largest and second largest number present in an array
C++ program to find the largest and second-largest numbers present in an array along with their location index on the array. This program first find the largest number by going through all the numbers in the array. It stores the index of the largest number on the variable pos1 and largest number is the largest variable. A second for loop is applied, which also check for the largest number. When it hits on the largest found by the first loop, it is bypassed using a continue statement and hence will get the second-largest number.
#include <iostream> #include <conio.h> using namespace std; void main() { int a[10], i, largest = 0, second_largest = 0, pos1, pos2; int n; cout << "Enter Number of elements :"; cin >> n; for (i = 0; i < n; ++i) { cout << "n Enter " << (i + 1) << "th Element :"; cin >> a[i]; } //Finding Largest for (i = 0; i < 10; ++i) { if (a[i] > largest) { largest = a[i]; pos1 = i; } } //finding second largset for (i = 0; i < 10; ++i) { if (a[i] > second_largest) { if (a[i] == largest) continue; //Ignoring largest in order to get second largest second_largest = a[i]; pos2 = i; } } cout << "nn Largest Number :" << largest << " at position " << (pos1 + 1); cout << "nn Second Largest Number :" << second_largest << " at position " << (pos2 + 1); getch(); return; }*Compiled using Visual Studio
UNIX Shell Programming – Complete Turtorial : Part 1
Lecture Note : Unix Shell Programming Part 1
Topics :-
Introduction to Unix – Architecture of Unix, Features of Unix , Basic Unix Commands – Unix Utilities:- Introduction to unix file system, vi editor, file handling utilities, security by file permissions, process utilities, disk utilities, networking commands – Text processing utilities and backupIntroduction to Unix
UNIX is a popular operating system in the engineering world and has been growing in popularity lately in the business world. Knowledge of its functions and purpose will help you to understand why so many people choose to use UNIX and will make your own use of it more effective.History of Unix
In 1965, Bell Telephone Laboratories joined an effort with the General Electric Company and Project MAC of the Massachusetts Institute of Technology to develop a new operating system called Multics. The goal of the Multics system were to provide simultaneous computer access to a large community of users, to supply ample computation power and data storage and to allow users to share their data easily, if desired. Although a primitive version of the Multics system was running on a GE 645 computer by 1969, it did not provide the general service computing for which it was intended, nor was it clear when its development goals would be met.In an attempt to improve Bell Laboratories’s programming environment, Ken Thompson, Dennis Ritchie and others sketched a paper design of a file system that later evolved into an early version of the UNIX file system. Thompson wrote programs that simulated the behavior of the proposed file system and of programs in a demand-paging environment and he even encoded a simple kernel for the GE 645 computer. Later he found that the program was unsatisfactory because it was difficult to control the space ship and the program was expensive to run. Thompson later found a little used PDP-7 computer that provided good graphic display and cheap executing power. Programming Space Travel for the PDP-7 enabled Thompson to learn about the machine, but its environment for program development required cross-assembly of the program on the GECOS machine and carrying paper tape for input to the PDP-7. To create a better development environment, Thompson and Ritchie implemented their system design on the PDP-7, including an early version of the UNIX file system, the process subsystem and a small set of utility programs. Eventually the new system no longer needed the
GECOS system as a development environment but could support itself. The new system was given the name UNIX.Although this early version of the UNIX system held much promise, it could not realize its potential until it was used in a real project. Thus, while providing a text processing system for the patent department at Bell Laboratories, the UNIX system was moved to a PDP-11 in 1971. The system was characterized by its small size: 16K bytes for the system, 8K bytes for user programs, a disk of 512K bytes, and a limit of 64K bytes per file. After its early success, Thompson set out to implement a Fortran compiler for the new system, but instead came up with the language B. influenced by BCPL. B was an interpretive language with the performance drawbacks implied by such languages, so Ritchie developed it into one he called C, allowing generation of machine code, declaration of data types and definition of data structures. In 1973, the operating system was rewritten in C. The number of installations at Bell Laboratories grew to about 25 and a UNIX Systems Group was formed to provide internal support.AT&T could not market UNIX as they have signed a Consent Decree with the Federal government in 1956. But they provided UNIX system to universities who requested it for educational purposes. In 1974, Thompson and Ritchie published a paper describing the UNIX system in the Communications of the ACM giving further impetus to its acceptance. By 1977, the number of UNIX system sites had grown to about 500, of which 125 were in the universities. UNIX systems became popular in the operating telephone companies, providing a good environment for program development, network transaction operations services and real-time services. In 1977, the UNIX system was first ported to a non-PDP machine, ie, it is made to run on another machine with few or no changes, the Interdata 8/32.With the growing popularity of microprocessors, other companies ported the UNIX system to new machines, but its simplicity and clarity tempted many developers to enhance it in their own way, resulting in several variants of the basic system. In the period 1977 to 1982, Bell Laboratories combined several AT&T variants into a single system, known commercially as UNIX System III. Bell Laboratories later added several features to UNIX System III, calling the new product UNIX System V and AT&T announced official support for System V in January 1983. However, people at the University of California at Berkeley had developed a variant to the UNIX system, the most recent of version of which is called 4.3 BSD for VAX machines. By the beginning of 1984, there were about 100,000 UNIX system installations in the world, running on machines with a wide range of computing power from microprocessors to mainframes and on machines across different manufacturers product lines. No other operating system can make that claim.Architecture of Unix

Unix Architecture The figure depicts the high-level architecture of the UNIX system. The hardware at the centre of the diagram provides the operating system with basic services. The operating system interacts directly with the hardware, providing common services to programs and insulating them from hardware idiosyncrasies. Viewing the system as a set of layers, the operating system is commonly called the system kernel or just the kernel emphasizing its isolation from user programs. Because programs are independent of the underlying hardware, it is easy to move them between UNIX systems running on different hardware if the programs do not make assumptions about the underlying hardware.Programs such as the shell and editors (ed and vi) shown in the outer layers interact with the kernel by invoking a well defined set of system calls. The system calls instruct the kernel to do various operations for the calling program and exchange data between the kernel and the program. Several programs shown in the figure are in standard system configurations and are known as commands, but private user programs may also exist in this layer as indicated by the program whose name is a.out, the standard name for executable files produced by the C compiler. Other application programs can build on top of lower-level programs, hence the existence of the outermost layer in the figure. For example, the standard C compiler, cc, is in the outermost layer of the figure: it invokes a C preprocessor, two-pass compiler, assembler, and loader (link-editor), all separate lower-level programs. Although the figure depicts a two-level hierarchy of application programs, users can extend the hierarchy to whatever levels are appropriate. Indeed, the style of programming favored by the UNIX system encourages the combination of existing programs to accomplish a task.Many application subsystems and programs that provide a high-level view of the system such as the shell, editors, SCCS and document preparation packages have gradually become synonymous with the name “UNIX system”. However, they all use lower-level services ultimately provided by the kernel, and they avail themselves of these services via the set of system calls.Features of Unix
Some useful facts concerning UNIX programs and files:· A file is a collection of data that is usually stored on disk, although some files are stored on tape. UNIX treats peripherals as special files, so that terminals, printers, and other devices are accessible in the same way as disk-based files.· A program is a collection of bytes representing code and data that are stored in a file.· When a program is started, it is loaded from disk into RAM. When a program is running, it is called a process.· Most processes read and write data from files.· Processes and files have an owner and may be protected against unauthorized access.· UNIX supports a hierarchical directory structure.· Files and processes have a location within the directory hierarchy. A process may change its own location or the location of a file.· UNIX provides services for the creation, modification and destruction of programs, processes and files.The main features of UNIX are listed below:· UNIX allows many users to access a computer system at the same time.· It supports the creation, modification and destruction of programs, processes and files.· It provides a directory hierarchy that gives a location to processes and files.· It shares CPUs, memory, and disk space in a fair and efficient manner among competing processes.· It allows processes and peripherals to talk to each other, even if they are on different machines.· It comes complete with a large number of standard utilities.· There are plenty of high-quality, commercially available software packages for most versions of UNIX.· It allows programmers to access operating features easily via a well-defined set of system calls that are analogous to library routines.· It is a portable operating system and thus is available on a wide variety of platforms.Basic Unix Commands – Unix file permissions, process utilities, disk utilities, networking commands
This section introduces the basic Unix commands. The commands which are introduced here are cancel, cat, cd, chgrp, chmod, chown, clear, cp, date, emacs, file, groups, head, lp, lpr, lprm, lpq, lpstat, ls, mail, man, mkdir, more, mv, newgrp, page, passwd, pwd, rm, rmdir, sty, tail tset, vi, wc etc.Obtaining an account in unix
You need to get an account for working with Unix. If you don’t have your own computer with Unix installed and working, you need to get an account to work with. This may be possible at your work location, the institute where you study etc. You need to contact the system administrator to get an account. The account will have a user id and a password to access the same.Logging in
In order to use a UNIX system, you must first log in with a suitable username – a unique name that distinguishes you from the other users of the system. Your user name and initial password are assigned to you by the system administrator or it is set to something standard if you bought your UNIX system. Use these to login to the system. For login, the system will show a screen asking for a login name with a prompt “login: “. There you have to type the username and then press ENTER key. It will prompt with the password “Password: “. Normally whatever you type here will not be shown since it is a secret. If you enter the correct user name and password, the system logs you in and shows a prompt that it is ready to take on commands from you. By convention, the prompt is dollar sign (“$”) or percentage sign (“%”) for normal users and hash character “#” for system administrator. These can be changed by the user, but these are the default values. When a command is issued, the shell executes the command and once the command execution is over, it comes back to the shell. It is again indicated by the prompt which the system shows.
cd command in Unix
The cd command is used for changing directory. If you issue this command without any parameter, it will go to the home directory. Home directory is the directory where you are positioned when you login. You can give a directory name also as a parameter for the cd command. The directory name you give can be relative or absolute. In a relative path, you specify where you want to go relative to where you are. In an absolute path, you specify the path starting with a slash “/” character to indicate the root filesystem. From root point onwards, you specify each directory in that order separated by a slash.Ex:cdcd /var/log/squidcd ../../var/log/squidShells
The $ or % prompt that you see when you first log into UNIX is displayed by a special kind of program called a shell – a program that acts as a middleman between you and the raw UNIX operating system. A shell lets you run programs, build pipelines of processes, save output to files, and run more than one program at the same time. A shell executes all the commands that you enter. The most popular shells are the Bourne shell, The Korn shell, the C shell and the Bourne Again shell. All these shells share a similar set of core functionality, together with some specialized properties. The Korn shell is a superset of the Bourne shell and thus users typically no longer use the Bourne shell as their login shell. Each shell has its own programming language. One reasonable question to ask is why would you write a program in a shell language rather than a language like C or Java? The shell languages are tailored to manipulating files and processes in the UNIX system, which makes them more convenient in many situations.date command
date [yymmddhhmm[.ss]]The date command prints the current system date. When run with no arguments, it displays the current date and time. If arguments are provided, date sets the date to the setting supplied, where yy is the last tow digits of the year, the first mm is the number of the month, dd is the number of the day, hh is the number of hours using 24-hour clock, and the last mm is the number of minutes. The optional ss is the number of seconds. Only a superuser may set the date.clear command
This command clears your screen.man command
The man command is used for obtaining online help. There are times when you are at your terminal and you can’t quite remember how to use a particular utility. Alternatively, you may know what a utility does but not remember what it’s called. You may also want to lookup some utility for the exact implementation on the particular installation. The UNIX system has a utility called man (short for “manual page”) that puts information at your fingertips.man [ [-s] section ] wordman –k keywordThe manual pages are on-line copes fo the original UNIX documentation, which is usually divided into eight sections. The pages contain information about utilities, system calls, fire formats and shells. When man displays help about a given utility, it indicates in which section the entry appears. The first usage of man displays the manual entry associated with word. A few versions of UNIX use the –s argument to indicate the section number. If no section number is specified, the first entry that man finds is displayed. The second usage of man displays a list of all the manual entries that contain keyword.stty command
The stty command is used to print and set the special characters for controlling the terminal. Some special characters or character combinations – they are also called metacharacters – are interpreted differently by UNIX. For example, after you start to execute a command in a shell, you want to stop execution of that command. You may press Ctrl-C (control key and C). This will close the program. Similarly, there are a number of such special combinations which control the terminal. The stty command can be used to print the current setting as well as set some of them. For printing the current settings, stty –a will do. The typical controls are erase (backspace one character), kill (erase all of the current line), flush (ignore any pending input and reprint the line), susp (suspend the process for a futre awakening), intr (terminate or interrupt the foreground job with no core dump), quit (terminate the foreground job and generate a core dump), stop (stop/restart terminal output), eof (end of input) etc.passwd command
The passwd command allows you to change your password. You are prompted for your old password and then twice for the new one. The new password may be stored in an encrypted form in the password file “/etc/passwd” or in a “shadow” file for more security. You can also use this utility to change the password of another user by specifying the userid “passwd userid”.Log out
For log out of the system, press the key sequence Ctrl-D which is end of input. That means, there is nothing more as input for the shell program which is running for you and hence it terminates. Alternatively, the command exit can be used which is valid for many shells.Some more commands
The command pwd can be used for displaying the current working directory.The command cat (contatenate) can be used for displaying the contents of a text file.The command ls can be used for listing the contents of a directory.The command more, page, head, tail can be used for displaying the contents of a text file.The command mv can be used to rename a file to another name. It can also be used to move one file from one directory to another directory.The command mkdir can be used to create a new directory.The command cp can be used to copy files and directories.The command vi is used to edit a text file.The cd command is used to change directory.The rm command can be used to remove a file.The rmdir command can be used to remove a directory.A text file can be printed using lpr command.The wc command can be used to count the characters, words and lines in a text file.The file command will help to identify what type of file is the input argument.The groups command will help to find out how many groups I am assigned to.The command chgrp can be used to change the current group to a new group.The command chmod can be used to change the permissions of a file.File handling utilities in Unix
Filtering filesegrep, fgrep grepThese are used for searching files for specific patterns.ls command is used for listing details about the files.Removing duplicate lines: uniqSorting files: sortComparing files: cmp, diff. cmp finds the first byte that differs between two files. diff displays all the differences and similarities between two files.Finding files: findgrep – Global Regular Expression Printer – helps to search for a pattern or expression in a text file. It helps to either print the matching lines or non-matching lines. The command grep is very useful to build text processing applications.cut – the command cut is used to selectively cut a column of output from a text file. The column can be decided based on the list of bytes, characters or fields. We can specify one and only one of bytes, characters or fields. List is made up on one range or many ranges separated by commas. For fields, TAB is the default delimiter. Any other delimiter can be specified by using option –d.Security by file permissionsFile permissions can be changed or set using chmod command. It works in either incremental mode or absolute mode. Incremental mode either adds or removes a particular permission or permissions. Absolute mode uses a code for setting permissions and then applies the same in one go.Incremental mode: chmod u+x mycommandschmod g-w mycommandschmod o-wx mycommandschmod [ugoa][+-=][rwxXst] <file> ; u – user, g – other users in the file,s groups, o – other users not in the file’s group, a – all, r – read, w – write, x- execute, s – set uid or groupid on execution, t – restricted deletion flag or sticky bit.chmod 755 mycommandsFile owner can be changed using chown command. You need to specify the owner and the file on which it has to be changed. It can also be used to change the group along with the owner.The file group can be changed using chgrp. Specify the new group and the file whose group is to be changed.Process utilities in Unix
The main command for listing processes is ps. It stands for process status. You will get a list of processes running now with the ps command. You will get information about a selection of the active processes. If you need a repetitive update of the selection, use top instead. By default, ps selects all processes with the same effective user ID as the current user and associated with the same terminal as the invoker. It displays the process ID, the terminal associated with the process (tty), the cumulated CPU time and the executable time. To see every process on the system, tryps –e OR ps –efWe can use the command top to see a continuous update of all processes. This is useful for system administrators to see which all processes take maximum CPU time, maximum memory etc.Disk utilities in Unix
Most commonly used disk utility is df and du. The command df is used to find out how much disk space is there, how much is being used and what percentage is free for each of the partitions and for selected partitions. By giving the option k, it will print the details in kilobytes instead of default blocks.The command du is used for finding out how much is the disk usage for a particular file in number of blocks. You may give a file, a directory or any combination of these as the argument.The command kill can be used for terminating a process. It takes as its argument the process id (pid) of the process. You have an option to send a specific signal while invoking the kill command. For example, you can send the SIGKILL (-9) which says kill the process under any circumstances. SIGHUP is used to send a reconfigure command to the service type (daemon) processes.Networking Commands in Unix
The commonly used networking commands are: finger, mesg, write, talk, wallThe finger command displays information about a list of users that is generated from the following sources: The users home directory, start-up shell and full name are read from the password file /etc/passwd.If the user supplies a file called .plan in the home directory, the contents of the file are displayed as the user’s plan.If the user supplies a file called .project, in the home directory, the contents of the file are displayed as the user’s project.If no user IDs are listed, finger displays information about every user that is currently logged on.The mesg command allows you to protect yourself from others contacting you. You may use it as “mesg [y|n]”. If you say “mesg n” the system will not allow others (except the administrator) to contact you using the communication utilities write, talk and wall.The write command allows you to send one line at a time to a named user. You have to use it as “write <userID> [tty]”. Then the receiver is show the message on his/her screen along with who is writing. The receiver could also write back to the sender.The talk utility allows you to have a two-way conversation across a network. The format is “talk user@host [tty]”. It displays a message on the user and that user has to respond with talk “fromUser@fromHost [tty]”.The wall command helps you to send a message to all users logged in. wall stands for “write all”. You start the wall command, it collects all text typed there until EOF and then sends it to all users logged in.The real networking utilities include ifconfig, netstat etc. The ifconfig command is used to configure the network interfaces. The netstat command can be used for listing the active network connections on the system.Text processing utilities and backup commands in Unix
Archives: cpio, tar and dumpcpio is handy for saving small quantities of data, but the single-volume restriction makes it useless for large backups. cpio copies files into or out of a cpio or tar archive, the archive can be another file on the disk, a magnetic tape or a pipe. GNU cpio supports the following archive formats: binary, old ASCII, new ASCII, crc, HPUX binary, HPUX old ASCII, old tar, and POSIX.1 tar. When extracting from archives, cpio automatically recognizes which kind of archive it is reading and can read archives created on machines with a different byte-order.In copy-out mode, cpio copies files into an archive. It reads a list of filenames, one per line, on the standard input, and writes the archive onto the standard output.In copy-in mode, cpio copies files out of an archive or lists the archive contents. It reads the archive from the standard input.In copy-pass mode, cpio copies files from one directory tree to another, combining the copy-out and copy-in steps without actually using an archive.tar allows you to save directory structures to a single backup volume. It is designed to save files to tape, so it always archives files at the end of the storage medium. The different options are concatenate (-A), create (-c), append (-r), list and test (-t), update (-u) and extract (-x).dump allows you to save a file system to multiple backup volumes. Dump is designed for doing total and incremental backups, but restoring individual files with it is tricky. A dump that is larger than the output medium is broken into multiple volumes.split allows us to split files into multiple pieces. We can specify the size of the fractions. It usually creates files with name of input file appended with .aa, .ab, .ac etc.